200 million enterprise, industrial, and medical devices affected by RCE flaws in VxWorks RTOS
Armis researchers have discovered 11 vulnerabilities (including 6 critical RCE flaws) in Wind River VxWorks, a real-time operating system used by more than two billion devices across industrial, medical and enterprise environments.

Collectively dubbed “Urgent11”, they are estimated to impact SCADA systems, elevators, industrial controllers, patient monitors and MRI machines, as well as firewalls, routers, satellite modems, VOIP phones and printers.
About Wind River VxWorks
VxWorks is a real-time operating system (RTOS), i.e., an OS that processes data and performs applications’ tasks within a strictly defined (extremely short) time.
This type of OS is mostly used in mission-critical devices and networking equipment, where speed, accuracy, response predictability and reliability are paramount.
“First released in 1987, VxWorks is one of the most mature operating systems still widely in use, and maintains a large number of its branches, due to the nature of the devices it operates and the difficulties in upgrading them,” the researchers noted.
“The actual extent of VxWorks devices is astonishing, including Siemens, ABB, Emerson Electric, Rockwell Automation, Mitsubishi Electronic, Samsung, Ricoh, Xerox, NEC, and Arris, among others.”
About the vulnerabilities
The “Urgent11” vulnerabilities (CVE-2019-12255 to CVE-2019-12262) reside in IPnet, VxWorks’ TCP/IP stack, which was acquired by Wind River through its acquisition of Interpeak in 2006.
They include six critical flaws that enable remote code execution and five that can lead to denial of service, leaking of information or errors. (More technical details are available here.)
Ben Seri, VP of Research at Armis, told Help Net Security that three of the eleven vulnerabilities have existed in the IPnet code prior to Wind River’s acquisition of Interpeak, but the rest of the vulnerabilities were introduced later on.
“The IPnet networking stack is a component of some versions of VxWorks, including end-of-life (EOL) versions back to 6.5. Specifically, connected devices leveraging older standard VxWorks releases that include the IPnet stack are impacted by one or more of the discovered vulnerabilities,” said Arlen Baker, Wind River Chief Security Architect.
“The latest release of VxWorks is not affected by the vulnerabilities, nor are any of Wind River’s safety-critical products that are designed for certification, such as VxWorks 653 and VxWorks Cert Edition. To date, there is no indication the Urgent/11 vulnerabilities have been exploited in the wild.”
He also noted that those impacted make up “a small subset” of their customer base, and primarily include enterprise devices located at the perimeter of organizational networks such as modems, routers, and printers, as well as some industrial and medical devices.
Exploitation potential
The vulnerabilities can be exploited by attackers to take control over a device situated either on the network perimeter or within it.
“Even a device that is reaching outbound to the internet could be attacked and taken over. Alternately, an attacker who has already managed to infiltrate a network can use Urgent/11 to target specific devices within it, or even broadcast an attack capable of taking over all impacted VxWorks devices in the network simultaneously,” Armis researchers shared.
“It is important to note that in all scenarios, an attacker can gain complete control over the targeted device remotely with no user interaction required, and the difference is only in how the attacker reaches it.”
Ben Seri and Dor Zusman will present the vulnerabilities at Black Hat USA 2019 and will demonstrate real-world end-to-end attacks on three VxWorks-based devices: a SonicWall firewall, a Xerox printer and a patient monitor.
According to the researchers, an attacker with an Internet connection can launch a direct attack with a specially crafted TCP packet and take control over all Internet-connected SonicWall firewalls at once, potentially roping them into a botnet and compromising the networks behind them.
In the “attack from within the network” scenario, an attacker could breach all vulnerable devices at once by broadcasting malicious packets throughout the network. For example, in an industrial setting, the attacker could take control over Programmable Logic Controllers running vulnerable VxWorks versions and disrupt production.
Demo videos of the attacks can be found here.
Attack prevention and mitigation
Armis disclosed the vulnerabilities to Wind River, which created patches and disseminated them to manufacturers of affected devices in June.
SonicWall and Xerox have already pushed out security updates for their firewalls and printers; other manufacturers will surely follow.
Wind River has released a security alert that includes information about the vulnerabilities, patches and mitigation options.
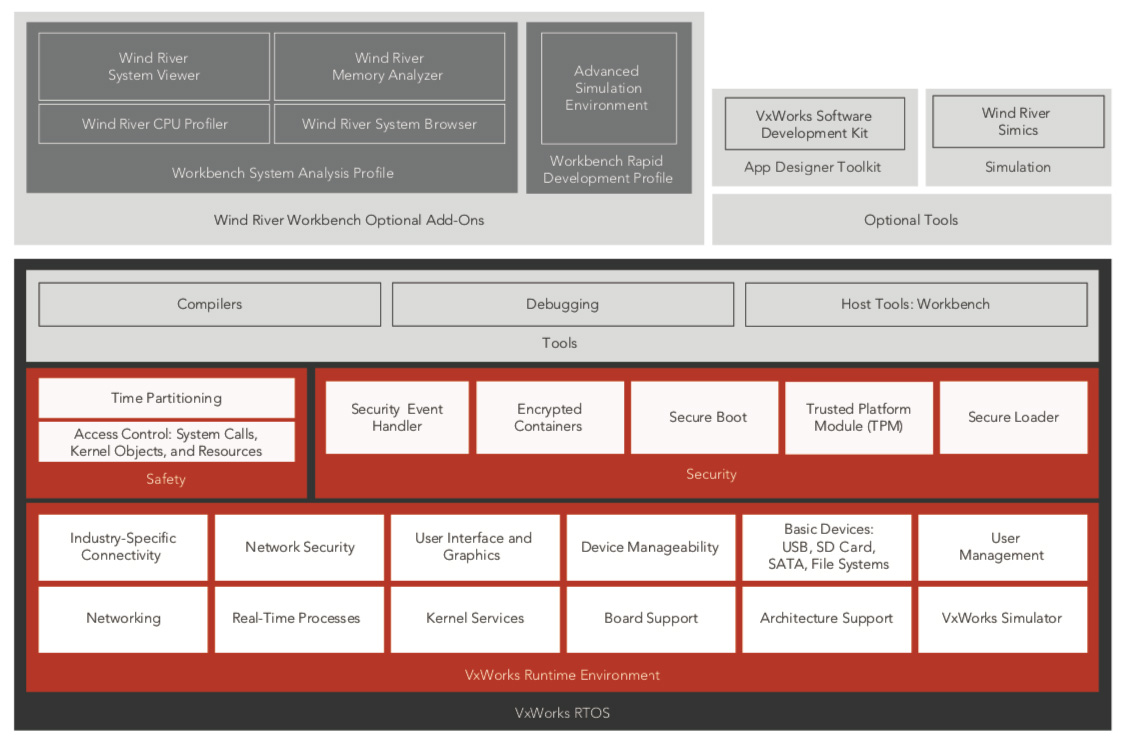
The company has provided patches for previous versions of VxWorks and have released a new version (VxWorks 7 SR0620) on July 19 that includes fixes for the discovered vulnerabilities. They have also detailed built-in security features that can be leveraged to protect against the identified vulnerabilities.
Organizations are advised to check whether they have vulnerable devices on their networks, patch them and shield them via network controls as best they can. Armis researchers also advise monitoring the behavior of all vulnerable devices for indications of compromise.
“Security appliances can and should be used to detect any attempts using Urgent/11 vulnerabilities,” Seri noted.
“Armis will be providing guidelines on how such mitigations can be put in place – such as firewall rules, and IDS signatures. In addition, Armis’ solution is already prepared to detect any attempt to exploit Urgent/11, and also identify all devices in organizations’ network that are using vulnerable versions of VxWorks – and drive users to update their devices.”
Additional considerations
Prior to Wind River’s acquisition of Interpeak, its TCP/IP stack was broadly licensed to and deployed by a number of other RTOS vendors. Since some of the discovered vulnerabilities date back prior to the acquisition, it’s possible they are still present in those deployments.
It’s also interesting to note that prior to the discovery of these vulnerabilities, only 13 CVEs have ever been listed by MITRE as affecting VxWorks, and none as severe as these.
“VxWorks’ uncharted nature stems from the fact that it is closed sourced, making it more difficult to inspect, and the fact that it is an RTOS, which has received less attention from the research community as it does not operate consumer devices,” the researchers noted.
“Wind River cares and is serious about security, but coding in a bug-free fashion is an impossible feat. For this reason it is important to research the lesser known operating systems such as VxWorks, especially when they are used so widely in over 2 billion devices,” Seri added.
“Some of the discovered vulnerabilities are very elusive, and are almost impossible to detect with automated tools. So from time to time, the work of vulnerability researchers can help uncover such vulnerabilities.”

UPDATE – 09:27 AM PT
Wind River told Help Net Security that they don’t believe the number of affected devices estimated by Armis (200 million) is accurate. A Wind River spokesperson told us: “Given the small subset of our customers impacted, along with the fact that VxWorks has built-in security features that protect against the vulnerabilities when enabled, we think millions is the best/most accurate way to characterize the number of affected devices.”