Cyber crooks continue to exploit COVID-19 for their malicious schemes
A time of chaos is a time for opportunity for unscrupulous individuals and groups, and COVID-19 is seemingly an unmissable boon for cyber crooks.
We’ve already covered a variety of COVID-19-themed scams, phishing attempts, hoaxes and malware delivery campaigns, but new and inventive approaches are popping up daily.
The latest schemes and scams that exploit COVID-19
Proofpoint researchers have observed COVID-19 being used as a pretext in BEC scams:

“BEC attacks are often delivered in stages. The first email sent is typically innocuous, meaning that they do not contain the attacker’s end goal. The attackers craft plausible scenarios in hopes the recipient will reply. Once they’re on the hook, the attacker will send their true ask. (I need you to buy gift cards, wire transfer funds, etc.),” the researchers explained.
“These coronavirus-themed BEC attacks often come with spoofed display names, which are likely real people known to the recipient. In the body of this message, the actor attempts to eliminate the possibility of voice-verification, in hopes of ensuring a higher success rate, by saying their phone is ‘faulty at the moment.'”
They’ve also spotted an assortment of fake notices impersonating doctors and local health agencies and institutions (aimed at the general population), as well as more targeted emails aimed at enterprises (employees), such as fake internal emails for credential phishing attacks impersonating the organization’s president, IT staff, risk manager, and so on.
Scammers are also trying to make media and advertising companies spread URLs of scammy websites to their audience – they offer money for the placing of the URL in a prominent place (e.g., on top of their most recent YouTube video description).

Malvertising campaigns and extortion
There has also been a spike in malvertising campaigns on coronavirus-themed news stories, delivering malicious Flash Player updates.
ESET researchers have spotted COVID-19-themed extortion emails:
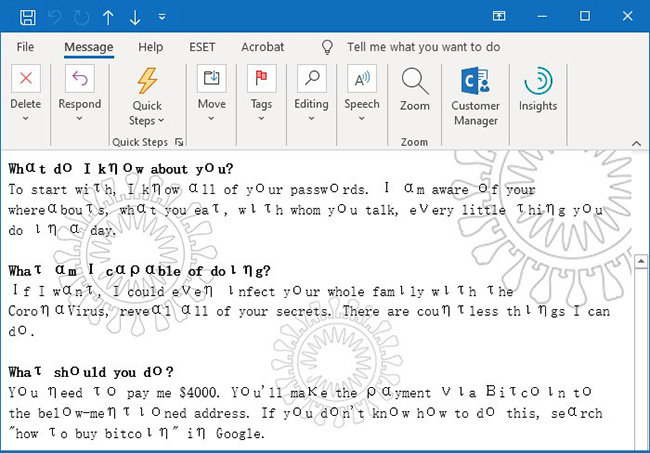
The sender is threatening to infect every member of the recipient family’s “with the Coronavirus” if he or she doesn’t deliver $4000. To make the threat more believable, the scammer uses leaked passwords in an attempt to create the impression that they know a lot about the recipient.
SpyCloud researchers have been keeping an eye on popular online criminal forums and have noticed:
- A threat actor advertising a service in which they craft coronavirus-focused scam letters and scam sites for customers
- A threat actor sharing instructions for cracking and taking over meal-kit delivery accounts, to take advantage of the fact that many people are ordering food online while attempting to practice social distancing. Another threat actor is offering to sell stolen meal-kit delivery codes.
Finally, with many, many people around the world losing their job due to the current situation, Brian Krebs says that cyber criminals have already started trying to trick them into becoming money mules. The pretext? They would be collecting and transmitting donations for an international “Coronavirus Relief Fund.”