Qualys VMDR 2.0 with TruRisk: Taking vulnerability management to the next level
In this interview for Help Net Security, Mehul Revankar, VP of Product Management & Engineering for VMDR at Qualys, talks about Qualys Vulnerability Management, Detection and Response (VMDR) 2.0 with TruRisk.
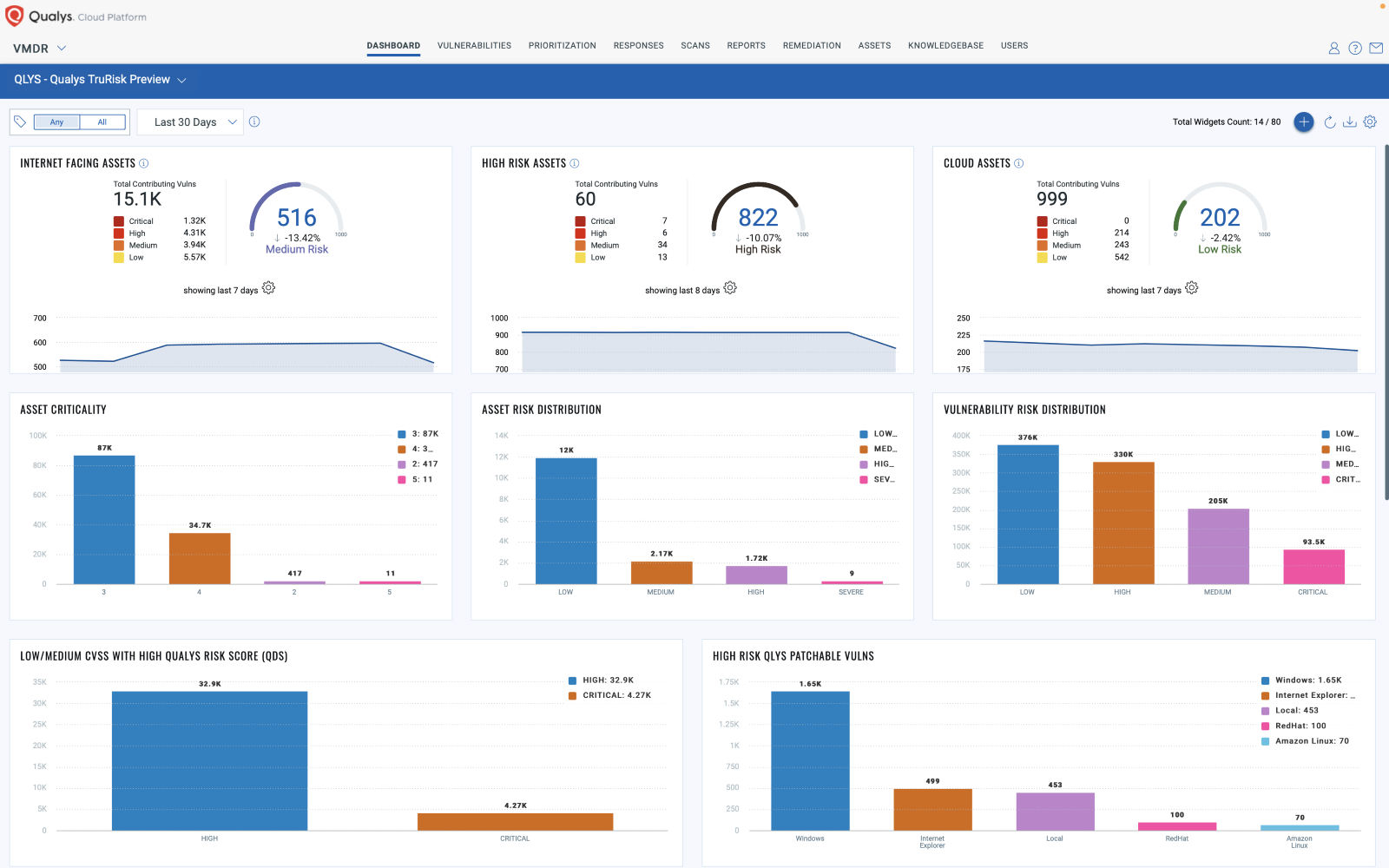
The solution gives unprecedented insights into an organization’s unique risk posture along with the ability to use drag and drop workflows to orchestrate responses.

Qualys announced Vulnerability Management Detection and Response 2.0 with TruRisk. Tell us more about the new capabilities, what can security and IT teams do with it?
Today’s organizations face increasing numbers of catastrophic breaches, internet-shaking vulnerabilities, nation-state-backed attacks, and a severe rise in ransomware – with Verizon’s DBIR 2022 reporting 13% YoY increase, a rise as big as the last five years combined.
Governments around the world are starting to make significant moves to defend against hacking gangs and continue to evolve alongside new legislation and increased cyber protocols. However, even with the heightened focus on protecting digital assets, bad actors have had a head start, and organizations are still reporting unease in their ability to ward off ongoing threats.
VMDR 2.0 with TruRisk was developed based on customer conversations to surface what tools were needed to uplevel their cyber security programs focused on risk. We found that what they needed most was the ability to prioritize and respond to the most pressing threats posing the highest risk to their organization. New product capabilities include:
- Track Business Context-based Cyber Risk – Comprehensively quantify risk across attack surfaces such as vulnerabilities, misconfigurations and digital certificates correlated with business criticality and exploit intelligence from hundreds of sources, including Shodan’s attack surface exposure data to proactively measure, track and communicate risk.
- Quickly Remediate at Scale – Rule-based integrations between VMDR and ITSM tools such as ServiceNow ITSM and JIRA, along with dynamic vulnerability tagging, automatically assign remediation tickets to prioritized vulnerabilities.
- Receive Preemptive Attack Alerts – External threat intelligence, from more than 180,000 vulnerabilities and 25 plus threat and exploit intelligence sources, is natively correlated with vulnerabilities and misconfigurations to proactively alert teams on vulnerabilities exploited by malware or those used in an active malicious campaign known to target your industry.
- Automate Workflows – Qflow technology, built into the Qualys Cloud Platform, delivers drag and drop visual workflows to automate time-consuming and complex vulnerability management tasks such as performing vulnerability assessments for ephemeral cloud assets as they are launched or alerting for high profile threats or quarantine high-risk assets saving valuable resources and time.
Cyber risk is becoming part of the business risk equation. What does your approach to cyber risk management include? How does it differ from what other vendors are offering?
No matter the difference in size, geography or industry – for today’s CISOs, managing cyber risk is job one.
With the VMDR 1.0 introduction in 2020, Qualys brought the four core elements of vulnerability management into a seamless workflow to help organizations efficiently respond to threats. Qualys is again changing the vulnerability management game with its VMDR 2.0 with TruRisk.
Qualys VMDR with TruRisk differs from other vulnerability management solutions in that it helps quantify risk across vulnerabilities, assets and groups of assets – helping organizations proactively reduce risk exposure and track risk reduction over time. It does this by considering multiple factors – exploit code maturity, active exploitation of the vulnerability, the criticality of the asset, its location etc. – so that organizations can gain a holistic view of their environment and focus efforts on fixes that will reduce their overall risk. Differentiating enhancements include:
- Allowing organizations to kickoff remediation workflow: This addition of automated workflows brings an orchestration engine to the vulnerability management space that no one else has done before.
- Automated prioritization: Automatically de-prioritizes vulnerabilities if compensating controls are in force, tracks risk reduction trends over time, and helps organizations measure and report on the effectiveness of their cybersecurity program across hybrid environment.
- New integrations: Actions like superseding patches, configuration fixes or workarounds, paired with the ability to orchestrate remediation directly from the ITSM tool, help close vulnerabilities faster and reduce the mean time to remediation.
Another unique factor of the product is the comprehensive threat and exploit intelligence which includes vulnerability intelligence for 180+ vulnerabilities tracked across 25+ different threat intelligence sources. These insights feed straight into the VMDR solution – guiding customers on imminent and rising threats.
Qualys enables customers to not only stay afloat but be more proactive and improve overall resiliency. How?
The doubling of disclosed vulnerabilities over the last five years, the speed at which vulnerabilities are weaponized, and the IT and cyber talent shortage, have left teams struggling to wade through a mountain of vulnerabilities with no way to fix them all. Security and IT teams need a new systematic approach to cut through the noise and prioritize fixing the most critical vulnerabilities to reduce risk in their environment.
But vulnerability management should not be prioritized based on CVSS scores alone. Out of the universe of 185,446 known vulnerabilities, only 29% have exploits available, just 2% have weaponized exploit code and threat actors are actively leveraging only 0.16%. TLDR: Cyber risk is much more achievable by focusing on the issues that present the highest threat to your environment.
Qualys’ approach to risk and vulnerability management moves beyond simply sharing a laundry list of vulnerabilities. It helps organizations prioritize and create remediation plans with risk-based vulnerability management. This gives security and IT teams shared context and the ability to create workflows to quickly align and respond to threats.
We think our customer, Brian Penn, manager Security Posture at Aflac says it best, “Qualys VMDR with TruRisk has helped us improve our program by providing additional context to threat and risk, better identifying high risk vulnerabilities, some of which the common vulnerability scoring system (CVSS) had previously rated as low or medium severity. It was eye opening to see that some of the identified assets posing the highest organizational risk were not always being immediately detected. The transparency of the rating algorithm also made it easy to justify prioritization and get all relevant security and IT stakeholders aligned and move quickly to remediate the risk.”
When will customers be able to try out Qualys VMDR 2.0 with TruRisk?
Qualys VMDR with TruRisk has been in beta for the past few months with several customers– including Fortune 500 insurance organization, Aflac and dental insurance company Dentaquest – testing out the new features. Over sixty Qualys customers were part of the beta program. Qualys VMDR with TruRisk helped customers prioritize up to 45.53% fewer critical vulnerabilities – with many organizations able to reduce real risk by over 51.10%.
Qualys VMDR with TruRisk will be generally available for all existing and prospective customers in late June. Organizations can sign up for a free trial.