New infosec products of the week: March 17, 2023
Here’s a look at the most interesting products from the past week, featuring releases from Atakama, Elevate Security, Hornetsecurity, HYPR, and ReversingLabs.


Hornetsecurity VM Backup V9 protects users against ransomware threats
VM Backup V9 has an easy-to-use, intuitive interface that gives individuals full control, allowing them to monitor and manage all Hyper-V and VMware VMs from a single console. V9 can now handle larger infrastructure setups. Its overhauled backup repository optimises disk space, ensuring more robust long-term storage.


ReversingLabs adds secrets detection capabilities to SSCS platform
ReversingLabs has unveiled new secrets detection features within its Software Supply Chain Security (SSCS) platform. It enables teams to securely control the release of software via the detection of software supply chain threats, malware, malicious behaviors, tampering, and secrets exposures


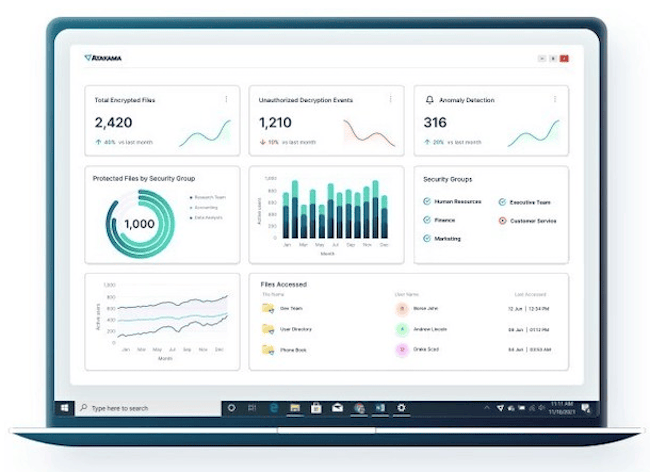
Atakama Enterprise protects unstructured data against exfiltration
Atakama unveiled its new Multifactor Encryption platform, Atakama Enterprise, featuring the Atakama Intelligence Center. Atakama’s Multifactor Encryption combines Distributed Key Management (DKM) with the proven concept of multi-device authentication for a progressive security solution that challenges the status quo of conventional data protection.

HYPR launches Enterprise Passkeys for Microsoft Azure
HYPR announced its newest offering, Enterprise Passkeys for Microsoft Azure. This new technology turns any smartphone into a FIDO2 virtual security key, providing authentication flexibility, user convenience and security while eliminating the complexity and cost of a hardware security key.


Elevate Identity enables security teams to automate customization of conditional access policies
Elevate Security released Elevate Identity, its SaaS offering for Identity and Access Management (IAM) Professionals that integrates Elevate’s user risk profiling capability with IAM tools such as Cisco Duo, Crowdstrike Falcon, and Microsoft Azure AD to add a full 360° perspective of each individual’s cyber risk to the authentication and authorization process.

