Machine identities outnumber humans 109 to 1
Organizations manage an average of 109 machine identities for every human identity. AI agents account for a growing share of those identities, with companies expecting AI agent growth of 85% over the next 12 months. Machine identities are projected to increase by 77%, and human identities by 56%, based on data from Palo Alto Networks’ 2026 Identity Security Landscape report.
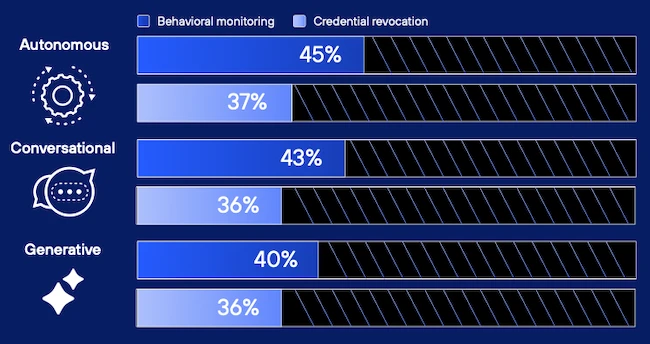
Which identity security controls does your organization apply across the AI agent lifecycle? (Source: Palo Alto Networks)
Most of them can explain the purpose of their AI agents, while far fewer can define what those agents can access, how access is limited, when permissions are revoked, or which systems can inherit that access.
AI agents and machine identities already reach financial records, personally identifiable information, operational technology, and core business systems. Respondents said AI agents should operate under least privilege principles with restricted access and tighter controls.
Organizations lack controls for AI agents
Environments still lack behavioral monitoring, credential revocation, and shutdown mechanisms for AI agents. Excessive or misused access can become a security issue quickly because these systems operate at machine speed.
They continue to rely on permanent privileged access instead of just-in-time controls. AI agents, workloads, connectors, and service accounts continue to add identities and permissions across cloud and on premises systems.
The data shows a gap between how leadership views security controls and what security teams experience in practice. C-suite executives believe their companies successfully enforce least privilege because they focus primarily on human access and overlook non-human identities. Security practitioners disagree because machines and automated systems manage a growing share of operations.
Managing this environment requires detailed, real-time control across identities, sessions, and systems, and organizations do not have that capability. To maintain operations, they often leave broad access rights in place for machines and rely on human oversight to reduce risk.
Privilege sprawl widens the identity gap
Human identities represent a smaller share of total identities across enterprise environments. Individual accounts still control a growing number of workflows, applications, and systems. A single login can invoke agents, trigger workflows, move data, and reach sensitive environments. Attackers continue to target those accounts because identity controls weaken after authentication.
Survey respondents said human identities often retain access beyond what their roles require. Local administrator rights and ungoverned process elevation on endpoints create paths for credential dumping and browser token theft.
Endpoint least privilege reduces the number of users capable of turning a compromised session into lateral movement or data access.
Fragmented controls across identity, privilege, endpoint, and machine identity systems also create operational pressure. Organizations grant broad access early in deployment cycles and remove permissions later.
Authentication does not stop post-login abuse
Identity related breaches continue to expose fragmentation across enterprise environments. Security teams often correlate evidence across multiple consoles with incomplete context during investigations.
Unit 42 examined more than 750 cyber incidents in 2025. In 87% of those cases, investigators needed evidence from two or more distinct sources to establish what happened. Complex incidents required as many as 10 evidence sources.
Fragmented identity systems also slow detection and response operations. Security practitioners reported that fragmented tools add an average of 12 hours to identity related incidents.
Environments treat authentication as the primary security control and provide limited protection after login. Service accounts and machine identities already manage trusted access across systems, but organizations lack visibility into their permissions and activity.
Single sign-on and MFA help secure logins, but they do not control what users, tokens, connectors, or automated systems can access after authentication. More than half of participants said they cannot consistently enforce least privilege access for service accounts across cloud, SaaS, and on premises systems.
They continue to manage stale accounts, unmanaged service accounts, and excessive permissions across cloud and on premises infrastructure. Former employees, legacy systems, and third party integrations often retain access longer than required.
Vendor reduction alone does not resolve those visibility and control gaps.
Trust weakens across machine driven environments
Identity systems process a constant stream of requests, tokens, sessions, certificates, and machine actions. Security practitioners increasingly recognize limits in static trust models and login focused defenses.
Attackers use AI to collect open source intelligence from social media platforms and corporate directories. That information supports the creation of synthetic identities and convincing access activity.
Hard coded secrets, OAuth tokens, certificates, and machine credentials remain distributed across enterprise environments. Overexposed or overtrusted credentials can remain active long after the operational need expires.
TLS certificate management continues to create operational strain. Certificate renewal and monitoring require centralized visibility, automation, and crypto agility. Firms rely on manual processes for certificate operations and continue to report PKI security challenges.
NIS2 and DORA continue to connect identity security practices with regulatory standing, partnership requirements, and cyber insurance expectations. Insurance requirements also influenced identity security investments during the past 12 months.
Companies are also dealing with a widening gap between automated attacks and human response times. AI models can identify vulnerabilities, map attack paths, and generate exploit code faster than many security operations can respond.
Identity controls remain one of the few defenses capable of responding in real time when vulnerabilities remain unpatched. Those controls include limiting standing privileges, identifying hidden access paths, and enforcing just in time access.