Why SOCs are moving toward autonomous security operations in 2026
The modern security operations center faces a crisis of scale that human effort cannot fix. With alert volumes exponentially growing and threat actors automating their attacks, organizations must pivot to autonomous SOC strategies. This shift to AI-driven defense is the only way to survive the operational realities of 2026.
The mathematical impossibility of legacy defense
We need to be honest about the state of the traditional SOC. It is failing. It is not failing because our analysts are lazy or unskilled. It is failing because the math no longer works.
In late 2025, the average mid-market enterprise security team processed over 4,000 alerts per day. Even a fully staffed team of seasoned tier-one analysts cannot investigate that volume with any degree of accuracy. The result is a dangerous game of probability where teams are forced to tune out “noisy” signals just to keep the queue manageable.
Attackers know this. They rely on it.
The operational blindness caused by this alert fatigue is not hypothetical. It is the direct cause of the National Public Data breach in 2024. In that incident, attackers did not use a zero-day exploit to gain access. They simply lived in the blind spots between disconnected security tools. They moved slowly. They harvested credentials. They exfiltrated nearly 3 billion records over several months.
The security tools likely saw pieces of this activity. The firewall saw data leaving. The endpoint protection saw a process spawn. But without a unified brain to connect those signals, the alerts were likely dismissed as low-priority noise. This is the cost of manual triage in an automated age.
The algorithmic adversaries
The threat landscape has shifted fundamentally in the last eighteen months. We are no longer just fighting human hackers typing on keyboards. We are fighting non-humans and their software.
Adversaries now use AI to automate the entire attack lifecycle. They use large language models to craft perfect phishing emails that bypass traditional filters. They use automated scripts to scan for vulnerabilities across thousands of targets simultaneously.
Most alarmingly, we have seen the weaponization of deepfake technology. The Arup incident in early 2025 serves as a grim warning. Attackers used AI-generated video and audio to impersonate a CFO during a live video conference. They convinced an employee to transfer $25 million to fraudulent accounts.
This attack succeeded because it bypassed the human layer of defense. The employee trusted their eyes and ears. A traditional SOC, relying on manual verification, had no chance to intervene in time.
However, an Autonomous SOC Operations model would view this differently. It would not look at the video. It would look at the telemetry. It would seem that the “CFO” was logging in from an unmanaged device. It would see the impossible travel speed from their last known location. It would flag the anomalous transaction request immediately. The machine does not get tricked by a deepfake. It trusts only the data.
Why tool sprawl is killing visibility
The typical security stack has become a tangled mess of point solutions. Organizations run an average of 28 distinct security tools. Each one has its own dashboard. Each one has its own query language. Each one generates its own format of logs.
This fragmentation creates what we call the “swivel-chair” effect. Analysts waste precious minutes copying IP addresses from a firewall log to paste them into a threat intelligence feed. They jump between the EDR console and the identity provider to verify a user.
This friction is where the attackers win.
By the time a human analyst correlates a network anomaly with an endpoint alert, the attacker has already moved laterally. The dwell time, the time an attacker sits inside a network before detection, remains stubbornly high for organizations relying on manual correlation.
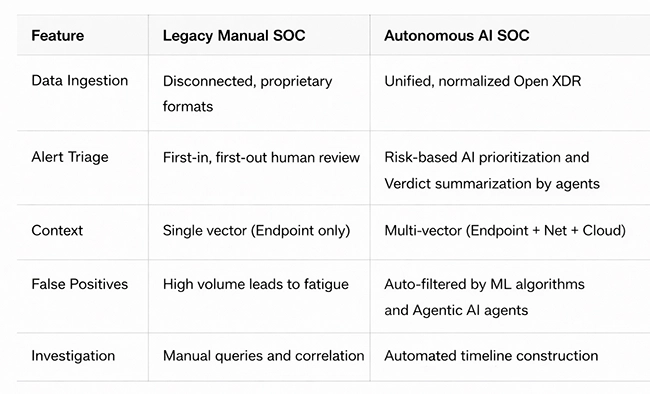
This drives the adoption of advanced SOC platforms that are built on Open XDR architectures. These platforms do not just collect logs. They ingest telemetry from every vector. They take data from the cloud, the network, the endpoint, and the identity provider. Then they normalize it into a standard format.
This unification is the prerequisite for autonomy. You cannot have an autonomous system if your data is speaking twenty different languages. Once the data is unified, the machine can begin to think.
The mechanics of autonomous detection
The shift toward autonomy changes the role of the “detection” phase. In a legacy model, detection relies on writing static rules. “If X happens, alert Y.”
But rules are brittle. They generate false positives. They miss new variations of attacks.
Autonomous systems use machine learning (ML) to establish baselines. They learn what “normal” looks like for every user and device in the organization. They know that the marketing director never logs in at 3 AM to access the engineering database. They know that a web server should not be initiating outbound connections to an unknown IP range.
When these anomalies occur, the system does not just send an email. It scores the risk. It correlates the anomaly with other weak signals across the environment.
Breaking the silos
This correlation capability is critical for stopping complex attacks like the Salesforce/Drift OAuth abuse cases seen recently. In those attacks, the initial compromise often looked like a legitimate login. The malicious activity, creating new OAuth tokens, looked like administrative work.
A siloed tool sees these as separate, benign events. An autonomous engine sees the pattern. It recognizes the sequence of “Login from new ISP” followed immediately by “High-privilege token creation” as a high-fidelity threat.
The speed of automated response
Detection is useless without action. The most significant advantage of SOC automation is the collapse of the response window.
We measure success in mean-time-to-respond (MTTR). For many organizations, this is measured in days or weeks. In an autonomous environment, it is measured in minutes or seconds.
When a high-fidelity threat is confirmed, the system can execute pre-approved playbooks. These are not reckless actions. They are carefully defined containment steps based on frameworks like NIST SP 800-207.
If a ransomware strain is detected on a laptop, the system does not wait for an analyst to return from lunch. It isolates the device from the network immediately. If a user account shows clear signs of compromise, the system revokes their active sessions and forces a password reset.
This speed is the difference between a minor IT ticket and a headline-grabbing breach. It stops the bleeding before the infection can spread.
Solving the talent crisis
There is a persistent fear that AI will replace the security analyst. This view is short-sighted. The goal of the autonomous SOC is not to replace humans. It is to save them.
The cybersecurity industry faces a global shortage of over 3 million professionals. We simply cannot hire enough people to man the walls. The people we do hire are burning out at record rates. They did not enter this field to stare at progress bars and close false positive tickets. They entered it to hunt threats.
Autonomous operations remove the drudgery. The machine handles the data processing. It handles the initial triage. It handles the compilation of evidence.
This elevates the role of the analyst. Instead of being a data janitor, the analyst becomes a threat hunter. They become a strategist. They spend their time investigating the complex, nuanced incidents that require human judgment. They proactively hunt for threats that have not yet triggered an alarm.
This makes the job more fulfilling. It helps organizations retain their top talent. It allows a team of five to do the work of a team of twenty.
The strategic path forward
The transition to autonomous security operations is no longer a “nice to have.” It is a necessity for survival.
The adversaries have already automated their offense. They are using AI to scale their attacks and find our weak points faster than ever before. If our defense relies on manual speed and human stamina, we will lose.
Organizations must view this transition as a core strategic investment. It is an investment in resilience. It allows the security posture to scale with the business. It decouples risk from headcount.
By adopting an autonomous architecture, leaders can finally answer the question “Are we secure?” with confidence. They can move from a posture of reactive panic to one of proactive control. The tools exist. The methodology is proven. The only variable remaining is the willingness to change.