Microsoft flips Windows Autopatch to default hotpatch security updates
Microsoft is changing the default behavior in Windows Autopatch so that hotpatch security updates are enabled automatically for eligible devices managed through Microsoft Intune or the Microsoft Graph API starting with the May 2026 Windows security update.
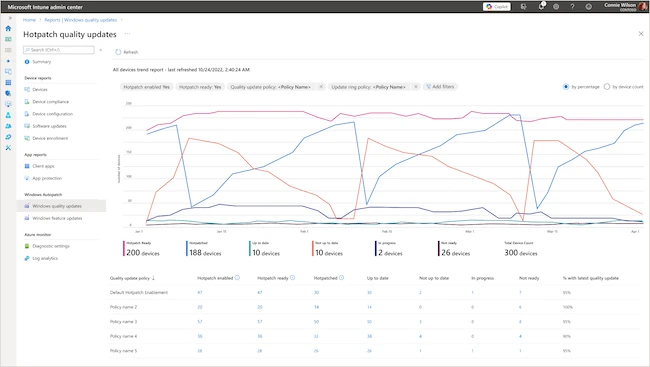
Windows Autopatch is a Microsoft-managed service that automates updates for Windows and Office. It also lets IT administrators pause updates and roll them back if devices fail to meet performance targets after installation.
Introduced about a year ago, hotpatch allows security fixes to take effect immediately without requiring a restart and previously required manual activation by administrators. According to Microsoft, eliminating restart delays significantly accelerates device patching.
“Applying security fixes without waiting for a restart can help organizations reach 90% compliance in half the time, while remaining in control,” the company said.
Devices that meet hotpatch prerequisites and install the April 2026 baseline security update will begin receiving hotpatch updates in May 2026.
The default setting applies only to devices not already assigned to a quality update policy, while existing configurations, including hotpatch settings, update rings, and deferral preferences, remain in effect.
If an enrolled device is not on the latest baseline, Autopatch will first install that baseline update, which requires a restart. After that, future security fixes will apply without reboots.
Microsoft recommends keeping hotpatch updates enabled, though organizations can opt out specific device groups or their entire tenant if they’re not prepared. The tenant opt-out setting becomes available on April 1, 2026. Because April is a hotpatch baseline month, deployments will not begin until May 11.
IT admins can find more details about the change and enrollment instructions in the company’s blog post.