Wi-Fi roaming security practices for access network providers and identity providers
Public Wi-Fi roaming networks carry authentication credentials across multiple administrative boundaries, and the protocols governing that process vary widely in their security properties. The Wireless Broadband Alliance published a set of guidelines that specifies which authentication, encryption, and credential-handling practices operators should apply to networks running Passpoint and OpenRoaming.
“What this work shows is that, by applying established best practices across authentication, encryption, identity privacy, signaling and federation governance, Wi-Fi can provide the level of security and consistency needed for modern roaming and offload use cases,” said Cameron Dunn, Assistant VP, In-Building Solutions, AT&T Services.
Authentication methods and what Passpoint certifies
Authentication methods and what Passpoint certifiesPasspoint-certified equipment must support five EAP method and credential-type combinations. Certificate-based authentication uses EAP-TLS. SIM and USIM credentials use EAP-SIM, EAP-AKA, or EAP-AKA’. Username and password credentials use EAP-TTLS with MSCHAPv2 as the inner method.
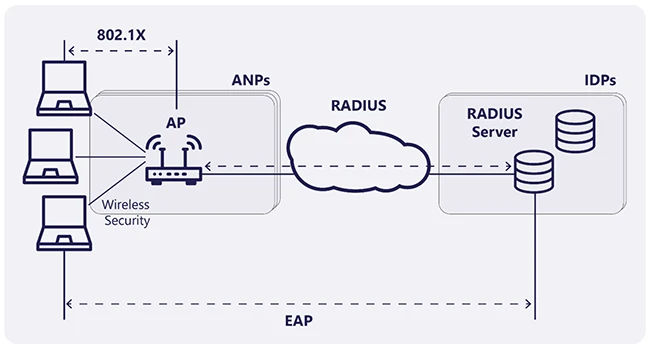
Overview of the 802.1X/EAP Process (Source: WBA)
MSCHAPv2 requires NThash storage on the AAA server, which is no longer considered secure for storing user credentials. EAP-TTLS with PAP as the inner method is the most widely deployed option in use. Despite PAP transmitting the password in plaintext at the application layer, the outer TLS tunnel encrypts that traffic before it crosses the network. Server certificate verification, by Common Name or Subject Alternative Name, is required during phase one of EAP-TTLS to ensure credentials reach the correct AAA server.
EAP-TLS is the most secure method in the Passpoint set, with one significant limitation: under TLS 1.2, client certificate details can be observed by access network providers and hub operators brokering the authentication exchange. Using TLS 1.3 eliminates that exposure. For deployments requiring TLS 1.2, carrying the EAP-TLS credential as an inner method inside an EAP-TTLS 1.3 tunnel protects the certificate from observation.
Identity privacy and the NAI
In Passpoint roaming, the Network Access Identifier transmitted as the RADIUS User-Name must carry no personally identifiable information. The user portion of the NAI must be replaced with the word “anonymous,” for example “anonymous@example.com,” with the realm portion used for routing to the appropriate identity provider.
For SIM-based methods, temporary pseudonym identities and fast re-authentication usernames provide privacy protection during subsequent authentication exchanges. The realm in SIM-based NAIs follows the format @wlan.mncXXX.mccYYY.3gppnetwork.org, which means the Mobile Network Code and Mobile Country Code remain visible.
For session tracking and incident handling, operators should use the Chargeable-User-Identity attribute returned by the identity provider. The CUI value must be unique per end-user and access network provider combination, with the underlying keys refreshed at minimum every 48 hours and at most every two hours.
Encryption: WPA2, WPA3, and the transition mode problem
Data encryption relies on WPA2-Enterprise and WPA3-Enterprise specifications. WPA2 mandates Counter Mode with CBC-MAC Protocol using AES with 128-bit keys and blocks. WPA3 extends key size to 256 bits and adds Galois/Counter Mode Protection.
WPA3 mandates Protected Management Frames, which protect management frames including authentication, de-authentication, association, and disassociation messages. In the 6 GHz band used by Wi-Fi 6E and Wi-Fi 7, WPA3 support is mandatory.
Transition Mode allows legacy devices to connect using older protocols on networks that support newer ones. The guidelines identify this as a security risk: it slows urgency to upgrade and can lead operators to believe their networks use current security practices when they do not.
Physical and backhaul security for access network providers
Access points should be deployed in physically inaccessible locations, such as high on walls or ceilings, and in tamper-proof enclosures. Access points typically do not store security information locally, so physical compromise of a unit does not expose stored credentials.
Management and user traffic between access points and controllers should be encrypted via secure tunneling or VPN. VPN backhaul for high-bandwidth standards like Wi-Fi 6, 6E, and 7 can degrade performance, and local breakout architectures with on-premises gateways mitigate that latency.
For RADIUS transport, the original RADIUS protocol specified in RFC 2865 is insecure because much of its content travels in plaintext and certain attribute values are hashed with MD5, which is easily compromised. RADIUS/TLS and RADIUS/DTLS are the recommended secure transport replacements, with a fallback to VPN protection when those protocols are unavailable.
Quantum computing on the horizon
IEEE 802.11 formed a Post Quantum Cryptography study group in April 2025. Current asymmetric key algorithms used in Wi-Fi security, including RSA and Elliptic Curve Cryptography, will become vulnerable once quantum computers are capable of attacking them. EAP-TLS version 1.3 and EAP-AKA can be enhanced through IETF work to support quantum-resistant Key Encapsulation Mechanisms.
Other 802.11 key exchange mechanisms, including Fast Initial Link Setup, Simultaneous Authentication of Equals, and Opportunistic Wireless Encryption, require IEEE-level enhancements to address post-quantum risks.

Download: CIS Benchmarks March 2026 Update