Cargo theft malware actor spent a month inside a decoy network before researchers pulled the plug
Proofpoint researchers executed a malicious payload from a threat actor known to target trucking and logistics companies in late February 2026, doing so inside a decoy environment. The environment stayed compromised for more than 30 days, long enough for researchers to watch the actor work through their tools, scripts, and decisions beyond the initial break-in.
The attacker had previously been documented targeting transportation carriers through compromised load board platforms, which are online marketplaces connecting shippers and freight brokers with motor carriers. This engagement revealed what happens after that initial foothold is established.
How the infection started
On February 27, 2026, after compromising a load board platform, the actor delivered a malicious payload via email to transportation carriers inquiring about fraudulent advertised loads. The payload was a Visual Basic Script file. When executed, it downloaded and ran a PowerShell script, installed the ScreenConnect remote access tool, and displayed a decoy broker-carrier agreement to mask the activity.
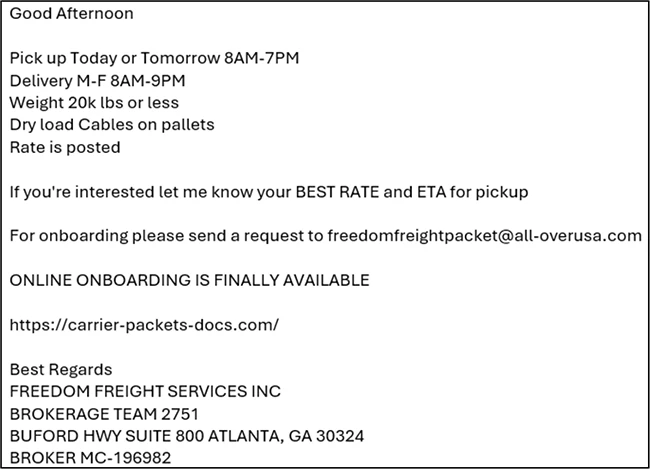
Email content sent after responding to a fraudulent load posted on a load board (Source: Proofpoint)
Stacking remote access tools for redundancy
Once inside, the actor installed four separate ScreenConnect instances, Pulseway RMM, and SimpleHelp RMM over the course of the intrusion. Running multiple remote management platforms simultaneously points to deliberate redundancy, preserving access in case one tool gets flagged or disabled.
A signing service nobody had seen before
The fourth ScreenConnect instance, downloaded in late March, was different from what the actor had deployed before.
The attacker used an existing ScreenConnect session to launch a PowerShell script that submitted a ScreenConnect installer to an external signing service. That service re-signed the installer with a valid but fraudulent code-signing certificate and hosted the signed file on attacker-controlled Amazon S3 infrastructure.
After installation, the script replaced ScreenConnect binaries originally signed with revoked ConnectWise certificates with versions carrying the new certificate, one Windows still recognized as trusted.
“In combination, these actions allowed the attacker to establish and maintain persistent remote access while actively circumventing certificate revocations, security warnings, and trust‑based endpoint controls. By laundering trust through an external signing service and replacing revoked vendor‑signed binaries, the attacker preserved long‑term, stealthy access and reduced the likelihood of user awareness or control‑based detection,” Proofpoint researchers explained.
Hands-on reconnaissance
About three days after gaining access, an operator manually browsed to PayPal through the victim’s browser. Eight days in, the actor ran a PyInstaller-packed binary to scan for browser extension and desktop cryptocurrency wallets, exfiltrating results to attacker-controlled Telegram bots.
Over the course of the intrusion, the actor ran at least 13 PowerShell scripts, all aimed at figuring out whether the compromised machine belonged to someone with financial access. The scripts enumerated local user accounts and browser profiles, extracted browsing history from Chrome, Edge, Firefox, and Chromium variants, and searched for access to specific platforms. Targets included U.S. banks, money transfer services, online accounting platforms, interbank payment systems, freight brokerage platforms, and fleet fuel card providers.
The results were sent to Telegram bots for operator review.
What the reconnaissance signals
“This extended intrusion highlights how financially motivated threat actors targeting transportation organizations operate well beyond initial access, prioritizing persistence, reconnaissance, and credential harvesting to identify opportunities for financial exploitation across transportation and related financial platforms. Portions of this activity are also consistent with preparatory behavior observed in freight theft and cargo diversion operations,” Proofpoint researchers noted.
“Notably, the use of a signing‑as‑a‑service capability underscores a growing trend toward attacker use of legitimate trust mechanisms to evade detection.”

Webinar: The IT Leader’s Guide to AI Governance