Microsoft: Phishing campaign used fake compliance notices to compromise employee accounts
Phishers have been using fake workplace compliance notices to try to trick Microsoft account owners into signing in via a fake sign-in page, says the company’s Defender Research team.
The email campaign targeted more than 35,000 users across 13,000 organizations in 26 countries, but concentrated primarily on targets in the United States. Microsoft didn’t say how many fell for the lure and had their account compromised.
From inbox to account takeover
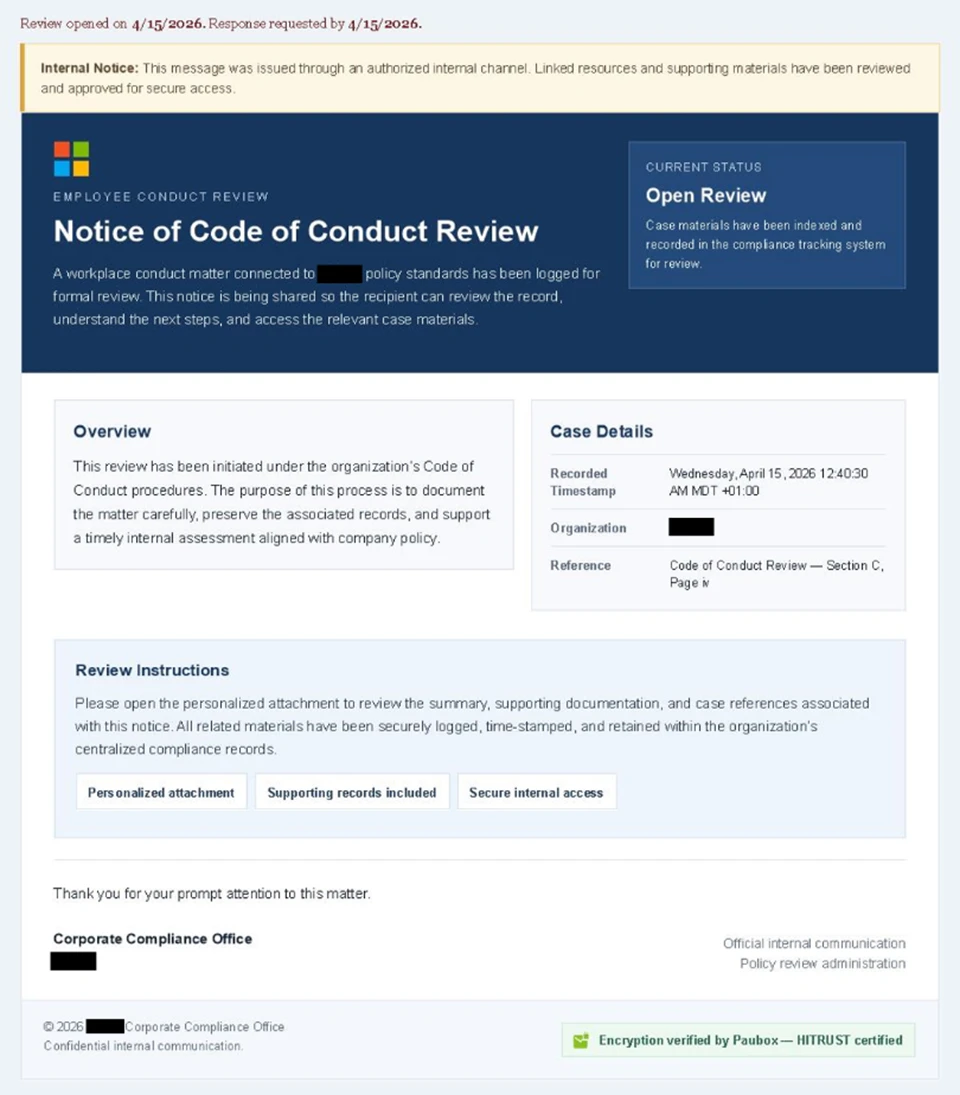
The campaign, which ran in waves between April 14 and 16, 2026, impersonated internal HR and compliance communications, sending emails with subject lines such as “Internal case log issued under conduct policy” and “Reminder: employer opened a non-compliance case log.”
Display names like “Internal Regulatory COC” and “Workforce Communications” gave the messages the appearance of legitimate internal communications. Each email also included a notice claiming the message had been “issued through an authorized internal channel” and that all links and attachments had been “reviewed and approved for secure access.”
Finally, a green banner at the foot of each email falsely indicated the contents had been encrypted using Paubox, a real service associated with HIPAA-compliant communications.
The phishing email (Source: Microsoft)
Victims who opened the attached PDF were directed to click a “Review Case Materials” link, which kicked off a complex multi-stage redirect chain.
They first encountered a Cloudflare CAPTCHA page, then were passed to another page telling them that account authentication was required to access encrypted case documents:
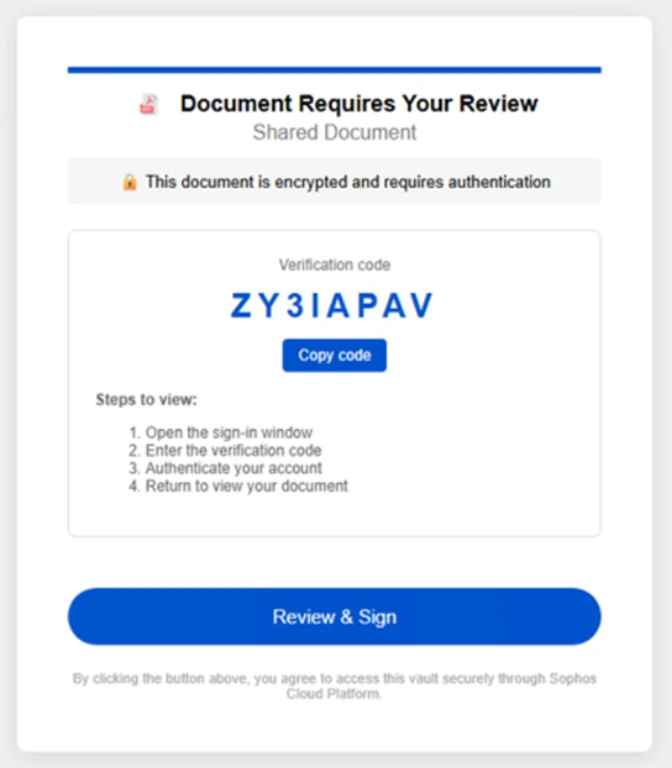
The page asking users to review and sign the prepared document (Source: Microsoft)
Clicking on the provided ‘Review & Sign’ button presented users with a sign-in prompt requesting their email address. After entering the address, they had to complete a second CAPTCHA, and then were redirected to a page saying that “all materials have been securely logged, time-stamped, and maintained withing the organization’s centralized compliance tracking system,” and asking them to sign in with their Microsoft account within five minutes (or the link will expire).
Once clicked, the “Sign in with Microsoft” button initiated an adversary-in-the-middle (AiTM) session. Access credentials and code-based authentication factors submitted into the fake sign-in page were silently proxied to the real one, allowing the attackers to intercept session tokens after authentication was completed.
These captured tokens allowed the attackers to access the victims’ account without knowing their password or possessing their second factor.
Built to deceive and bypass defenses
This sophisticated email campaign was designed to alarm, and “because the messages contained concerning accusations and repeated time-bound action prompts, the campaign created a sense of urgency and pressure to act,” Microsoft noted.
The attackers sent the emails using a legitime email delivery service, from multiple sender addresses using domains that are likely attacker-controlled, the researchers added. CAPTHA pages were used to prevent automated analysis and sandbox detonation.
“The campaign also varied its final destination depending on whether the victim was on a mobile device or desktop, indicating a level of technical sophistication beyond typical phishing operations,” they added.
Microsoft has urged organizations to deploy multi-factor authentication methods such as FIDO security keys or Windows Hello, which are not susceptible to AiTM token theft.
Other recommended mitigations include enabling Safe Links and Safe Attachments in Microsoft Defender for Office 365, turning on Zero-hour auto purge to retroactively remove malicious messages, and running phishing simulation training to help employees recognize social engineering lures of this kind.

Subscribe to our breaking news e-mail alert to never miss out on the latest breaches, vulnerabilities and cybersecurity threats. Subscribe here!