Anamarija Pogorelec

Google study finds LLMs are embedded at every stage of abuse detection
Online platforms are running large language models at every stage of LLM content moderation, from generating training data to auditing their own systems for bias. Researchers …
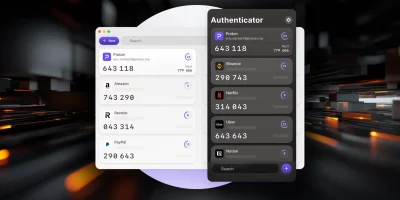
Product showcase: Proton Authenticator is an end-to-end encrypted, open source 2FA app
Proton Authenticator is a free and open-source two-factor authentication (2FA) app that generates time-based one-time passwords (TOTP) to help secure online accounts. It is …

CISOs grapple with AI demands within flat budgets
Security spending continues to edge upward across large organizations, though the changes remain gradual and tightly managed. The 2026 RH-ISAC CISO Benchmark reflects a steady …

Windows Security app gets Secure Boot certificate status indicators as 2026 expiration approaches
Microsoft’s Secure Boot certificates, issued in 2011, are approaching expiration in 2026. To help IT administrators track whether devices have received replacement …

Microsoft releases open-source toolkit to govern autonomous AI agents
AI agents can book travel, execute financial transactions, write and run code, and manage infrastructure without human intervention at each step. Frameworks like LangChain, …

Click, wait, repeat: Digital trust erodes one login at a time
Sign-up forms that drag on, login steps that repeat, and access requests that take longer than expected have become a normal part of using digital services. These moments …

New infosec products of the month: March 2026
Here’s a look at the most interesting products from the past month, featuring releases from Beazley, Bonfy.AI, Mend.io, Mimecast, NinjaOne, Novee, Intel 471, Singulr AI, …

AWS, Wasabi, Cloudflare, and Backblaze go head-to-head in new cloud storage test
Cloud storage buyers rarely get vendor-provided performance data that includes the vendor’s own weak spots. Backblaze’s Q1 2026 Performance Stats report, attempts …

OpenSSH 10.3 patches five security bugs and drops legacy rekeying support
OpenSSH 10.3 shipped carrying five security fixes alongside feature additions and a set of behavior changes that will break compatibility with older SSH implementations that …

Tracking drones with the 5G tower down the street
Drone detection in cities is expensive. Dedicated radar installations are cost-prohibitive at scale, cameras have limited range and stop working well at night, and LiDAR …

Microsoft adds high-volume email sending to Exchange Online
Organizations that rely on Exchange Online for internal communications have long needed a way to send large volumes of automated messages, such as payroll notifications, IT …

CIS Benchmarks March 2026 Update
The following CIS Benchmarks and CIS Build Kits have been updated or recently released. The Center for Internet Security has highlighted the major updates below. Each …
Featured news
Resources
Don't miss
- ClickFix campaign delivers Mac malware via fake Apple page
- Poisoned “Office 365” search results lead to stolen paychecks
- What vibe hunting gets right about AI threat hunting, and where it breaks down
- Health insurance lead sites sell personal data within seconds of form submission
- Claude helps researcher dig up decade-old Apache ActiveMQ RCE vulnerability (CVE-2026-34197)