
Websites can spy on user activity by analyzing SSD behavior
Websites have spent years collecting information about visitors through browser fingerprinting, tracking scripts, and other techniques designed to identify devices and monitor …
To counter cookie theft, Chrome ships device-bound session credentials
Cookie theft follows a well-established pattern. Infostealer malware infiltrates a device, extracts authentication cookies, and exfiltrates them to an attacker-controlled …

Firefox is getting a free built-in VPN
Mozilla is adding a free built-in VPN to Firefox, with the feature arriving in Firefox 149 on March 24. Privacy concerns often follow free VPN services, especially when …

Microsoft Edge 146 adds IP privacy and local network access controls
Microsoft Edge version 146 (Stable) became available on March 13, 2026, bringing updates to tracking protection, IP privacy, and enterprise network security policies. One …

Microsoft Edge 145 lands with major enterprise security upgrades
Microsoft has begun rolling out Edge 145 to the Stable release channel, adding several enterprise-focused security enhancements. The update is being deployed in phases, with …
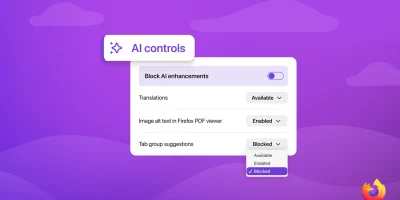
Firefox to let users manage and block AI features
Mozilla will add a set of controls in Firefox that let users manage and block GenAI features in the desktop browser. The controls will be included in Firefox version 148 on …

Grammarly and QuillBot are among widely used Chrome extensions facing serious privacy questions
A new study shows that some of the most widely used AI-powered browser extensions are a privacy risk. They collect lots of data and require a high level of browser access. The …

Fake browser crash alerts turn Chrome extension into enterprise backdoor
Browser extensions are a high-risk attack vector for enterprises, allowing threat actors to bypass traditional security controls and gain a foothold on corporate endpoints. …

Browser agents don’t always respect your privacy choices
Browser agents promise to handle online tasks without constant user input. They can shop, book reservations, and manage accounts by driving a web browser through an AI model. …
New “HashJack” attack can hijack AI browsers and assistants
Security researchers at Cato Networks have uncovered a new indirect prompt injection technique that can force popular AI browsers and assistants to deliver phishing links or …

Security gap in Perplexity’s Comet browser exposed users to system-level attacks
There is a serious security problem inside Comet, the AI-powered agentic browser made by Perplexity, SquareX researchers say: Comet’s MCP API allows the browser’s …

The browser is eating your security stack
Employees log into SaaS platforms, upload files, use AI tools, and manage customer data from a single tab. While the browser has become the enterprise’s main workspace, it …
Featured news
Resources
Don't miss
- Dutch police disrupts botnet composed of 17 million devices
- New infostealer reaches enterprise devices through FortiClient EMS vulnerability
- LinkedIn-themed phishing abuses Adobe’s A/B testing platform
- The behavioral signals that sharpen Trojan malware detection
- Zapier exploit chain shows how known anti-patterns compose into critical risk