conferences

EU organizations buckle under rising compliance pressure
Cybersecurity governance in the EU is shifting under expanding frameworks such as NIS2 and DORA, while AI raises new questions for security teams. What the future brings is …

Coinflow CISO on crypto payments security under AI pressure
Crypto payment firms sit near the top of the target list for advanced persistent threat groups, and the workload on their security leaders keeps growing. Malcolm Portelli, …

$20 per zero-day is already the WordPress plugin reality
Vulnerability researchers have spent the past year arguing about whether AI agents can find real bugs at scale or whether they mostly generate noise. A pipeline built in three …

Communicating cyber risk in dollars boards understand
In this Help Net Security interview, Nick Nieuwenhuis, Cybersecurity Architect at Nedscaper, explains why cybersecurity has not delivered the resilience that decades of …

RSAC 2026 is back, and the certificate automation gap is impossible to ignore
RSAC 2026 Conference marked a return to form, more vibrant and better attended than any show I can recall over the past decade. The audience was distinctly international, with …

Top product launches at RSAC 2026
RSAC 2026 showcased a wave of innovation, with vendors unveiling technologies poised to redefine cybersecurity. From AI-powered defense to breakthroughs in identity …
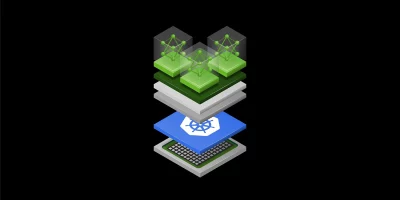
NVIDIA puts GPU orchestration in community hands
GPU-accelerated AI workloads now run on Kubernetes in the large majority of enterprise environments. Managing those workloads at scale has required specialized tooling that, …

Top must-visit companies at RSAC 2026
RSAC 2026 Conference is taking place at the Moscone Center in San Francisco March 23 – 26. With hundreds of booths, countless product demos, and nonstop buzz, navigating …

Turning expertise into opportunity for women in cybersecurity
Speaker diversity in cybersecurity has been a talking point for over a decade, with panels, pledges, and dedicated conference tracks failing to produce change. Stages still …

Span Cyber Security Arena 2026: Only 10 days left to secure early bird tickets
With preparations well underway, Span Cyber Security Arena 2026 is set to return for its third edition, bringing together domestic and international experts in cyber security. …

Span Cyber Security Arena 2026 to offer new perspectives on the development of cybersecurity
Through lectures, deep-dive presentations, best practice examples, and masterclasses, the focus of Span Cyber Security Arena 2026 will be on what strengthens our defense …

Cybersecurity research is getting new ethics rules, here’s what you need to know
Top cybersecurity conferences are introducing new rules that require researchers to formally address ethics in their work. Starting with the 2026 USENIX Security Symposium, …
Featured news
Resources
Don't miss
- Autonomous AI-driven worm can reason its way through corporate networks
- Only 11% of production agents pass the AI agent security bar
- A small Slovenian team handles 6,000 cyber incidents a year
- Agent Threat Rules: Open detection rule format for AI agent security threats
- Google fixes actively exploited Android vulnerability (CVE-2025-48595)