smartphones

New Android feature promises to spot deepfake scam calls
Android is introducing fake call detection to help protect users from impersonation scams. The feature can detect and flag suspected spoofed calls when both parties use Phone …
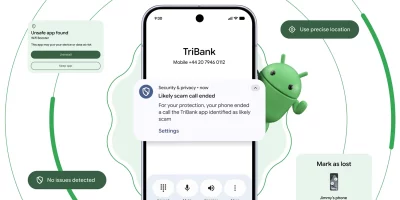
Android pushes new scam, theft, and AI protections in 2026 update wave
Phone scammers spoofing bank caller IDs have driven an estimated $980 million in annual losses worldwide, according to Europol. Android’s 2026 security roadmap takes …

CallPhantom Android scam reached 7.3 million downloads on Google Play
Scams targeting Android users in India and across the Asia-Pacific region have grown around a long-standing curiosity gap: the desire to look up call records tied to a phone …

Chrome on Android can now hide your exact location from websites
Google is improving location privacy features that give users more control over sharing their location. On Chrome for Android, users can now choose to share their approximate …

Google expands Android Binary Transparency to counter supply chain attacks
Supply chain attacks on mobile software have grown alongside the expanding role of phones in daily life, from payments to government IDs to AI features. Google is responding …

Phishing can masquerade as emergency alerts for disasters, researchers warn
Emergency alerts for disasters like earthquakes and tsunamis are messages we hope we never see, and we trust them when they arrive. Researchers have shown that this trust can …

Android app uses Bluetooth signals to detect nearby smart glasses
Smart glasses with built-in cameras are showing up in more public spaces, and a growing number of people want a way to know when one is nearby. An Android app called Nearby …

Samsung’s Galaxy S26 turns privacy into a visible and invisible feature
The Samsung Galaxy S26 series is out, offering plenty of security features that protect personal data while providing users with transparency and control over how their …

Google agrees to pay $135 million over Android data harvesting claims
Google agrees to pay $135 million to settle a proposed class action lawsuit brought by Android smartphone users over alleged unauthorized cellular data transmissions. After …

Samsung tackles shoulder surfing on Galaxy devices
Our phones hold our most personal details, and we use them everywhere. On the bus, in elevators, and while waiting in line, screens are often visible to people nearby. The …

Product showcase: Blokada for Android gives users control over network traffic
Blokada is a network privacy and ad-blocking application available on Android, iOS, Windows, macOS, and Linux. It is designed to reduce ads, block trackers, and limit unwanted …

AI vs. you: Who’s better at permission decisions?
A single tap on a permission prompt can decide how far an app reaches into a user’s personal data. Most of these calls happen during installation. The number of prompts keeps …
Featured news
Resources
Don't miss
- The architecture of subtraction: Why it’s time to erase the roads, not just map the traffic
- Treating AI agents like service accounts for federated query security
- Malware ships with bugs that defenders could use against it
- Qilin ransomware affiliate exploited Check Point VPN zero-day (CVE-2026-50751)
- CISA: Patch actively exploited SolarWinds Serv-U DoS vulnerability (CVE-2026-28318)