strategy

You can’t audit how AI thinks, but you can audit what it does
In this Help Net Security interview, Wade Bicknell, Head, IT Security & Operations, CFA Institute, discusses how CISOs can use AI while maintaining security and …

How the City of Toronto embeds security across governance and operations
In this Help Net Security interview, Andree Noel, Deputy CISO at City of Toronto, discusses how the municipality strengthens its cyber defense by embedding security into …

Building trust in AI: How to keep humans in control of cybersecurity
In this Help Net Security video, Rekha Shenoy, CEO at BackBox, takes a look at AI in cybersecurity, separating hype from reality. She explains why AI’s true value lies not in …

Life, death, and online identity: What happens to your online accounts after death?
The rapid technological advances of recent decades have transformed nearly every aspect of our lives. One major shift is that many of us now maintain extensive digital …
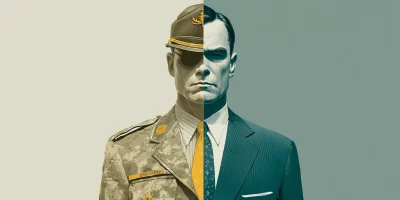
Why ex-military professionals are a good fit for cybersecurity
After years of working as part of a team, many military veterans look for work that still carries meaning, challenge, and purpose. Cybersecurity offers a new way to serve and …

Why cybersecurity hiring feels so hard right now
In this Help Net Security video, Carol Lee Hobson, CISO at PayNearMe, explores the realities behind the so-called cybersecurity “talent gap.” She explains why the issue is as …

Identifying risky candidates: Practical steps for security leaders
Effective insider threat defense begins with candidate vetting. Background checks and reference calls can confirm elements of an applicant’s history, but they rarely surface …

The solar power boom opened a backdoor for cybercriminals
Solar isn’t low risk anymore. Adoption has turned inverters, aggregators, and control software into attack surfaces capable of disrupting service and undermining confidence in …

Building a healthcare cybersecurity strategy that works
In this Help Net Security interview, Wayman Cummings, CISO at Ochsner Health, talks about building a healthcare cybersecurity strategy, even when resources are tight. He …

AI-generated images have a problem of credibility, not creativity
GenAI simplifies image creation, yet it creates hard problems around intellectual property, authenticity, and accountability. Researchers at Queen’s University in Canada …

From theory to training: Lessons in making NICE usable
SMBs may not have big budgets, but they are on the receiving end of many cyberattacks. A new study from Cleveland State University looked at how these companies could train …

Behind the screens: Building security customers appreciate
In this Help Net Security interview, Jess Vachon, CISO at PRA Group, discusses the company’s multi-layered defense against fraud and its commitment to protecting customer …