vulnerability management

Open-source security debt grows across commercial software
Open source code sits inside nearly every commercial application, and development teams continue to add new dependencies. Black Duck’s 2026 Open Source Security and Risk …
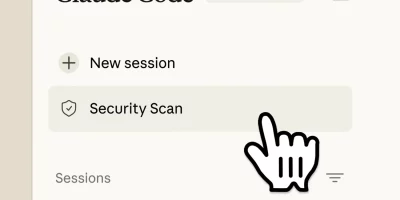
Claude Code scans, verifies, and patches code vulnerabilities
Anthropic brings Claude Code Security to Claude Code on the web through a limited research preview. Claude Code Security (Source: Anthropic) Claude Code Security analyzes code …

In GitHub’s advisory pipeline, some advisories move faster than others
GitHub Security Advisories are used to distribute vulnerability information in open-source projects and security tools. A new study finds that only a portion of those …

Don’t panic over CISA’s KEV list, use it smarter
In this Help Net Security video, Tod Beardsley, VP of Security Research at runZero, explains what CISA’s Known Exploited Vulnerabilities (KEV) Catalog is and how security …

Java security work is becoming a daily operational burden
Security teams in large enterprises already spend significant time tracking vulnerabilities across software supply chains, third-party libraries, and internal codebases. Java …

The hidden cost of putting off security decisions
In this Help Net Security video, Hanah Darley, Chief AI Officer, Geordie AI, talks about how putting off security risk decisions creates long-term costs that often stay …

CISA confirms exploitation of VMware ESXi flaw by ransomware attackers
CVE-2025-22225, a VMware ESXi arbitrary write vulnerability, is being used in ransomware campaigns, CISA confirmed on Wednesday by updating the vulnerability’s entry in …

Open-source attacks move through normal development workflows
Software development relies on a steady flow of third-party code, automated updates, and fast release cycles. That environment has made the software supply chain a routine …

Open-source malware zeroes in on developer environments
Open source malware activity during 2025 concentrated on a single objective: executing code inside developer environments, according to Sonatype. The focus reflected a broader …

The 2026 State of Pentesting: Why delivery and follow-through matter more than ever
Penetration testing has evolved significantly over the past several years. While uncovering exploitable vulnerabilities remains the core goal, the real differentiator today is …
LLMs can assist with vulnerability scoring, but context still matters
Every new vulnerability disclosure adds another decision point for already stretched security teams. A recent study explores whether LLMs can take on part of that burden by …

Why vulnerability reports stall inside shared hosting companies
Security teams keep sending vulnerability notifications, and the same pattern keeps repeating. Many alerts land, few lead to fixes. A new qualitative study digs into what …