ProtonMail restores services after epic DDoS attacks
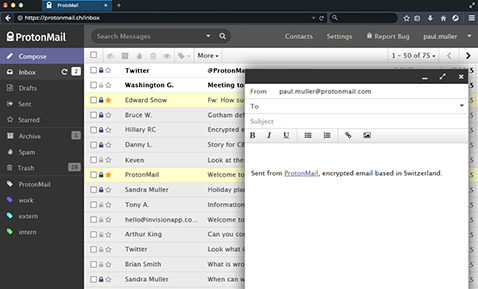
After several days of intense work, Switzerland-based end-to-end encrypted e-mail provider ProtonMail has largely mitigated the DDoS attacks that made it unavailable for hours on end in the last week.
The attacks have exceeded 100Gbps, and are still going on, but they are no longer capable of knocking ProtonMail offline for extended periods of time.
The first attacker, the Armada Collective is a new hacking group motivated by financial gain who demanded a ransom from the company. The second attack came from an unknown group. This second attack caused the bulk of the damage.
“Their sole objective was to take ProtonMail offline, at any cost, with no regards for collateral damage, and to keep us offline for as long as possible. The attack significantly disrupted our infrastructure and made email access impossible. This impacted over half a million users worldwide, including many journalists, activists, and dissidents who are active on our platform,” said Andy Yen, CEO of ProtonMail.
The ProtonMail community of users proved to be invaluable for the company. In fact, in just a few days, they donated over $50,000 to the company’s “defense fund”, providing the resources to resist further attacks against email privacy.
The Swiss-based secure email provider has selected Radware’s Attack Mitigation System (AMS) to help it take control of the situation and regain control of the mail service. Radware began working with ProtonMail on November 8th as part of their Emergency Response Service and service was restored shortly after.
“Advanced Persistent DoS (APDoS) is akin to the way bomber aircraft would jam radar systems many years ago – the type of attack is so varied and frequent that it becomes near impossible to detect them all, and more importantly difficult to mitigate them without impacting your legitimate web traffic. This technique will become a staple in the hacker’s armoury. The threat is real,” said Carl Herberger, Vice President for Security Solutions at Radware.