Energy sector IT pros overconfident in data breach detection skills
A new study by Dimensional Research evaluated the confidence of IT professionals regarding the efficacy of seven key security controls, which must be in place to quickly detect a cyber attack in progress. Study respondents included 763 IT professionals from various industries, including 100 participants from the energy sector.

According to the Department of Homeland Security, the energy sector faces more cyber attacks than any other industry. Despite the frequency in attacks, energy IT professionals participating in Tripwire’s survey were very confident in their ability to collect the data needed to detect a cyber attack.
For example, seventy-two percent of energy respondents believe they could detect configuration changes to endpoint devices on their organization’s network within hours, but over half (fifty-two percent) said their automated tools did not pick up all the necessary information, such as the locations, department and other critical details, needed to quickly identify unauthorized configuration changes to endpoint devices that can indicate an attack in progress.
“These results show that most security professionals are assuming they are doing the right things to secure their environments, but lack real world data to back up their assumptions,” said Travis Smith, senior security research engineer for Tripwire. “This highlights the importance of testing security controls to ensure they are functioning as expected. It’s not enough to install security tools throughout the environment. You must test the policies and procedures to be confident the controls in place will stop or detect real-world intrusions.”
Additional findings
- Seventy-three percent of energy respondents believe they could detect unauthorized software added to the organization’s network within hours, but only fifty-nine percent know exactly how long the detection process would actually take.
- Eighty-four percent of energy respondents believe they would receive alerts within hours if their vulnerability scanning systems detected unauthorized devices. However, over half (fifty-two percent) did not know how long it took to generate these alerts.
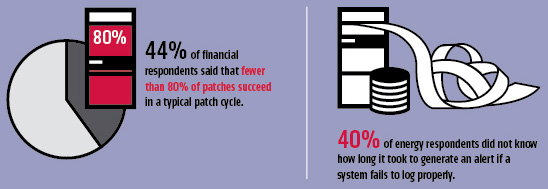
- Forty-four percent of energy sector respondents said that less than eighty percent of patches succeed in a typical patch cycle.
- Forty-percent of the respondents did not know how long it took to generate an alert if a system fails to log properly, however ninety-five percent assumed a report would be generated within hours.
“The energy sector has made significant improvements in securing their slice of the nation’s critical infrastructure, but broader adoption of security best practices is still lacking,” said Tim Erlin, director of IT security and risk strategist for Tripwire. “While dedicated security staff are intimately familiar with the deployed capabilities and gaps, IT at large is often working on assumptions of protection.”
The study is based on seven key security controls required by a wide variety of compliance regulations, including PCI DSS, SOX, NERC CIP, MAS TRM, NIST 800-53, CIS Top 20 and IRS 1075. These controls also align with the United States Computer Emergency Readiness Team (US-CERT) recommendations and international guidance, such as the Australian Signals Directorate’s Strategies to Mitigate Targeted Cyber Intrusions.
Recommendations and guidance
- Accurate hardware inventory
- Accurate software inventory
- Continuous configuration management and hardening
- Comprehensive vulnerability management
- Patch management
- Log management
- Identity and access management.
When implemented across an organization, these controls deliver specific, actionable information that is necessary to defend against the most pervasive and dangerous cyber attacks. Before any damage is done, it is vital for organizations to identify indicators of compromise quickly so that appropriate action can be taken.