Organizations still vulnerable to brute force attacks
While increases in malware are clearly a major threat to both enterprises and service providers, network complexity is creating its own vulnerability, according to Ixia.
The average enterprise is using six different cloud services, and network segmentation is increasing, yet 54% of enterprises are monitoring less than half of those network segments, and less than 19% of companies believe that their IT teams are adequately trained on the wide array of network appliances they are managing.
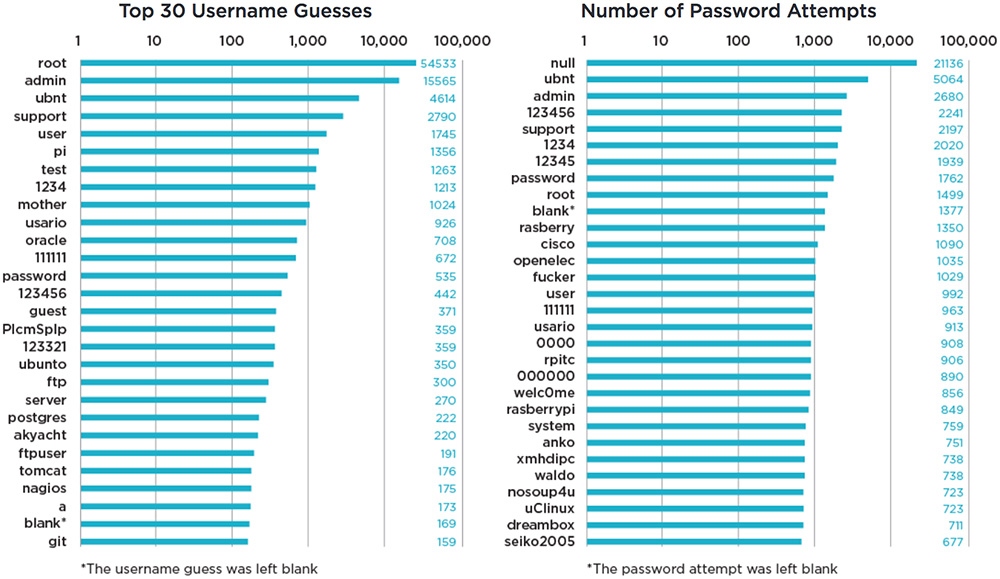
Top usernames and passwords
Gaining access to accounts is often done the old-fashioned way—brute force guesses, starting with the most obvious. It is shocking how many network accounts and devices contain default usernames and passwords. At the top of the list were usernames like “root” and “admin,” but also “ubnt,” which is the default username for AWS and other cloud service offerings that use Ubuntu. IoT was also a notable target with “pi” for Raspberry PI.
- The top 5 username guesses were: root, admin, ubnt, support, and user.
- The top 5 password guesses were: null, ubnt, admin, 123456, and support.
Malware or phishing?
Malware continued to dominate over 2016 but there were a few months — namely June, July, and August 2016 — during which ransomware phishing appeared to have outpaced conventional malware phishing.
- The top five phishing target websites globally were Google, Paypal, Facebook, Microsoft, and Alibaba.
- Adobe updates were found to be the most prevalent drive-by updates for delivering malware or phishing attacks.
Top exploited URI paths and content management systems
A uniform resource identifier (URI) is a string of characters used to identify a name of a resource, which can be interacted with via the web using specific protocols to try and exploit it.
WordPress URI paths were the two most exploited in 2016, showing how attackers are targeting sites built on the popular platform. The top exploited URI paths used for brute force WordPress logins were /xmlrpc.php and /wp-login.php. Ixia also saw many attempts to scan for the phpinfo() function and that most URIs attempted for attack were PHP based. WordPress was by far the most exploited content management system, with Joomla a distant second.