Fortanix Runtime Encryption: Protect sensitive applications and data in use

Encryption is an effective data protection control, however it’s use is currently limited to data at rest and data in motion. When, an application starts to run, it’s data in use is vulnerable to a variety of attacks including malicious insiders, root users, credential compromise, OS zero-day, and network intruders.
In this podcast recorded at RSA Conference 2018, Ketan Shah, VP of Products at Fortanix, talks about how the Fortanix Runtime Encryption platform leverages Intel SGX to enable general purpose computation on encrypted data without ever exposing plaintext application code or data.
Here’s a transcript of the podcast for your convenience.
Hello my name is Ketan Shah, I’m VP of Products at Fortanix and in this Help Net podcast I will be talking about how Fortanix Runtime Encryption delivers unmatched privacy for keys, secrets and more.
Our mission at Fortanix is to deliver deterministic security to applications. Encryption has been an effective control even in the cloud. Just like encryption protects data at rest and data in motion, Fortanix Runtime Encryption protects data in use even if the infrastructure is compromised, even if the root user access has been compromised.
So how do we do that? We leverage Intel SGX technology to run applications in secure enclaves. Our Runtime Encryption protects data in use without requiring any application modification. Runtime Encryption is being used to protect containers, keys and data processing. It delivers new levels of privacy and security control enabling highly sensitive workloads to run in the public cloud.

So let me talk about one of our first applications. When you look at the trend, modern enterprises have begun a historic migration to the public cloud. The migration is now entering a new stage. Organizations are looking to adopt even sensitive workloads in the cloud. Encryption remains the most effective control for protecting data in the cloud, and with encryption key management becomes more critical than ever. However key management has historically been the more complex part of encryption and with cloud migration it’s one of the more difficult puzzles to solve.
What choices do enterprises have? They’re kind of stuck between a rock and a hard place. Solutions were either designed before the cloud era, and are unable to serve distributed environments, or alternatively there are software based meaning they’re easy to use and agile, however do not offer the protection of hardware security modules or HSMs. As a result, enterprises end up making compromises between security, simplicity and scalability. Recognizing these trends, Fortanix has built Self-Defending Key Management Service (SDKMS), leveraging Runtime Encryption and Intel SGX.
The solution delivers unified HSM and key management capabilities. It offers HSM-grade security with software defined simplicity, and a cloud scale architecture. From a security standpoint, it protects the keys end to end – at rest, in motion and even in use.
SDKMS offers unmatched security, it provides complete protection of Runtime Encryption and Intel SGX, protecting the keys even when in use. It offers unified key management, HSM and tokenization capabilities, with all the operational simplicity of a single solution. Last but not least it provides deterministic security with complete user control of keys – nobody else, not the provider no external hacker can get access to your keys.
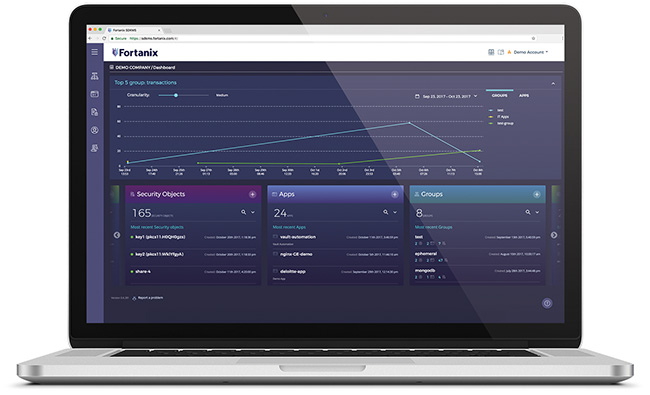
It does so with unparalleled simplicity. The solution offers a central dashboard and a web interface. It offers rich enterprise-grade access controls with single sign-on support for segregation of duties. It offers comprehensive auditing, integrating with your SIEM tools. For application consumption, it offers restful APIs to enable modern cloud apps, as well as mobile apps, and also offers traditional crypto interface support integrating with all your traditional solutions for encryption.
It’s built on a cloud scale architecture with a distributed scale out database that replicates automatically and delivers massive scalability. The solution is designed on an always-on high availability, disaster recovery and load balancing paradigm that eliminates operational complexity associated with such operations. It can scale to multiple sites and support multi-cloud environments.
Fortanix offers flexible consumption models for the solution. For private cloud consumption or for MSPs we offer a FIPS Level 3 appliance – FX 2200. This is an ideal building block for SDKMS. We also offer the solution as a software for customers that want to bring their own servers. Finally, the solution is purpose-built to be delivered as a cloud service, and for this offering we have partnered with Equinix, where we combine the best-of-breed cryptography software of Fortanix with Equinix’s interconnectivity and operations expertise. The solution is called Equinix SmartKey powered by Fortanix. This is a global SaaS HSM and key management service that simplifies data protection across any cloud.
Smart-Key is uniquely positioned to help customers with cloud adoption. As the data gets dispersed across on premise, public cloud and multiple clouds, what SmartKey does is it eliminates the need to purchase and deploy specialized hardware by replacing that traditional method with a private, secure and distributed SaaS capability.
It enhances security for multi-cloud, hybrid cloud and distributed environments by separating the encryption keys from the data. SmartKey also delivers low latency access for any application, any cloud leveraging the core competency of Equinix’s interconnectivity strengths.
How are organizations using SDKMS or SmartKey? Well one of the most common use cases is secure cloud adoption. Organizations using the public cloud for data processing typically encrypt that data at rest and in motion. However, they need a higher degree of protection for their keys, often its security requirements or compliance mandates that dictate that the keys must be kept separate from the data.
With our solution we empower organizations to remain in complete control of their keys, and organizations in lines of businesses themselves can empower their end customers and data owners to remain in control of those keys. We also seamlessly enable a multi-cloud journey. You find that a majority of organizations are using multiple providers or have hybrid IT, they either want to avoid the vendor lock-in, or would like to have the best-of-breed strategy for cloud adoption. Our solution enables a consistent implementation for encryption and key management policy for hybrid or multi-cloud.

The third use case is around securing custom code or business logic. We find strong demand to be able to run sensitive application logic or custom cryptographic schemes inside an HSM-grade trust boundary. Our solution is the only solution that can offer this high degree of customization. We do so empowering the organizations with a capability called Runtime Encryption Plugin – which is easy to develop, easy to configure and easy to deploy and consume.
Last but not least, we also see good adoption for GDPR and data privacy compliance. Our solution provides fine grained management of access controls to maintain data encryption keys in the same region, or same country, or within certain groups to support regulatory requirements as well as support data sovereignty requirements.
The mission at Fortanix is to enable secure adoption of the public cloud, whether hybrid or multi-cloud. Beyond HSM and key management, Fortanix Runtime Encryption also helps protect containers, machine learning data sets, analytics workloads, and databases in the cloud.
Fortanix won second place in the contest for Most Innovative Start-up at the RSAC Innovation Sandbox. We’re showcasing new capabilities for crypto agility; our Runtime Encryption Plugin empowers customers to secure business logic with a high degree of customization. We’re also showcasing new solutions that we continue to build-out, especially for bring your own keys to the cloud with integrations with providers like Google, AWS, Azure; as well as for key management solutions with providers such as VMware. If you’re interested to learn more please check out www.fortanix.com. Thank you for your time and interest.
