Organizations still use low levels or no automation of key security and incident response tasks
Most organizations understand that automation is the path to achieve optimal workflows in the face of staff shortages and alert fatigue.
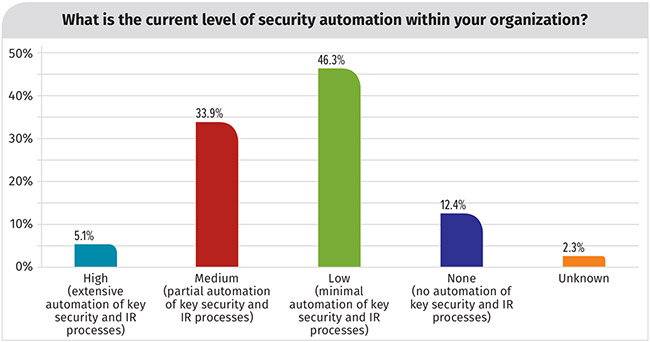
Yet, 59% of the D3 Security 2019 Automation and Integration Survey respondents indicated that their organizations use low levels or no automation of key security and incident response tasks.
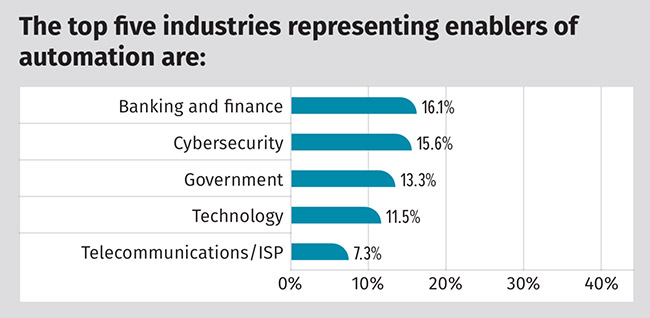
The study surveyed over 250 professionals with representation from five key industries that are considered enablers of automation (banking and finance; cybersecurity; government; technology; and telecommunications), who are directly involved in their organizations’ security operations and incident response (IR) practices.
“Making things look easy takes time and effort,” said Barbara Filkins, SANS analyst and author of the report. “Given the investment your organization is, or will be, making in time and resources needed to get the workflows correct, be sure to choose your SOAR technology wisely.”
As the study demonstrates, cybersecurity professionals are turning their focus to SOAR in their search for a solution that will not only answer the immediate need to overcome the current resource and skills gap, but also enhance security operations in the years to come.
The state of security automation
- Security monitoring and detection are the key activities supported by automation, with over 60% of respondents reporting a medium or high level of automation processes.
- Data protection and monitoring is next-highest, with nearly 50% of respondents reporting a medium or high level of automation processes.
- Not surprisingly, tools related to alerts and log analysis exhibit higher levels of automation than behavioral monitoring (profiling) or digital forensics.
- More than 57% of respondents anticipate changes to the focus of their use of automation in the next 12 months, while another 28% remain unsure.
- The top three factors affecting the level of investment in automation are budget and management support; skills required to integrate and operate tools; and amount of skilled staff.