ReversingLabs Malware Lab: Detect, classify, analyze, and respond to malicious files
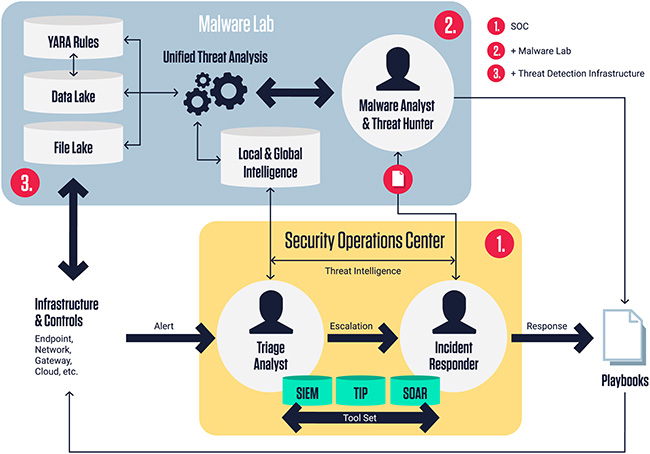
Designed to support modern security organizations increasingly delegating malware analysis to specific security operations (SOC) or development security operations (DevSecOps) experts, the ReversingLabs Malware Lab solution equips these teams with a unified threat analysis engine and console to rapidly detect, classify, analyze, and respond to malicious files and associated Indicators of Compromise (IOCs).
“Organizations are struggling to validate the effectiveness of their internal security controls and to respond to ever increasing quantities of actionable alerts. Homegrown and other complicated solutions have proven that responders are spending more time managing and integrating disparate technologies than addressing important alerts and incidents,” said Mario Vuksan, CEO at ReversingLabs. “At its heart, all SOC workflows, no matter how automated, require human analysis to provide context and inform their final decision. ReversingLabs Malware Lab is uniquely positioned as a commercial solution to give the highest quality of insight and decision support. Moreover, it is easy to deploy and integrate, while providing the industry’s most advanced file analysis and indicator enrichment across a wide span of threat vectors.”
Despite advances in layered security approaches, organizations are still struggling to sort through fragmented event data to achieve complete risk assessment and visibility. Organizations are transitioning their security programs to get more clarity in the face of a rapidly evolving threat landscape by establishing a malware analysis service. Such services centralize the analysis of suspected threats and the investigation of malware.
As a result, all alerts can be addressed and more proactive postures can be delivered within their defenses. In fact, a recent ReversingLabs survey of information security professionals reveals that nearly 40 percent of respondents agreed that their organization could improve security with a more formalized threat hunting and malware lab program.
ReversingLabs Malware Lab
Powered by ReversingLabs Titanium Platform, the ReversingLabs Malware Lab solution offers a unified threat detection and analysis infrastructure that enterprises can quickly implement and integrate across digital business, development, SOC and threat hunting processes.
Consumed in a hybrid cloud delivery model, organizations gain immediate access to split-second binary and threat analysis, safe file storage for malware, a data lake for metadata threat analytics and YARA portal for predictive threat matching.
Using ReversingLabs Malware Lab solution, organizations are able to quickly rationalize disjointed open source modules and expensive security tool sets to gain a new level of centralized security visibility and insights, all while integrating seamlessly into existing investigative workflows. It also gives security teams the ability to create a center of excellence that optimizes skill utilization and training to support operations, as well as the ability to improve processes with a centralized escalation point, universal service team and streamlined auditing response.
“By combining the best possible file analysis, safe storage for malware samples, searchable metadata repository of local analysis reports and global threat intelligence, the ability to tag content using YARA and cloud delivery in one enhanced seamless view, we give threat hunting teams access to all the resources we can bring to bear in one easy to use and manage package,” continued Vuksan. “ReversingLabs Malware Lab solution is uniquely capable in simplifying processes while helping mature security organizations to automate their analysis activities and quickly unpack binary objects, dissect file contents and extract and map human readable threat indicators that offer better insights to threats, including those in the software supply chain, which in turn helps to better direct appropriate responses.”
Ben Murphy, VP of Information Security, Deputy Chief Security Officer for Aflac U.S., the leading provider of supplemental insurance products in the United States, understands the importance of threat intelligence for mature security programs, and the need for dynamic and automated threat management for security effectiveness. Murphy adds, “Curated threat feeds can be a commodity. It’s the threat intelligence that’s well enriched, meaningful and trusted that’s valuable.”

ReversingLabs Titanium Platform
The ReversingLabs Titanium Platform powers it’s easy to use and commercially supported ReversingLabs Malware Lab solution, which includes:
Ease of Use: Commercially supported software package that utilizes best of breed technologies in an easy to use and integrated fashion, allowing defenders more time to focus on threat analysis and monitor security controls.
Unified Threat Analysis Platform: SOC analysts, malware researchers, hunters and application security professionals gain a centralized view and reporting into advanced threat analysis. Powered by unprecedented speed and scale to support large files, malware and supply chain analysis, the centralized workbench supports malware investigation, workflows, and threat hunting across all major platforms and file types. is. Unified binary and threat analysis, comprising automated static analysis and dynamic analysis (i.e. sandboxing technologies) capabilities, as well as analysis results from other key indicator sources within the platform, including network (URI/URL, IP, Domain) and certificate trust chains.
Safe Malware “Sample Locker” Storage: A file lake that stores malware samples in a secure, private location, with restrictive access. Archived samples are available for future research, threat hunting and training, with a detailed manifest of security context for navigating archived content.
Searchable Threat Intelligence Repository: A data lake that stores file metadata derived through static analysis, supporting advanced search and continuous monitoring. A definitive repository of local and relevant global intelligence used for enriching existing security controls and infrastructure with more explainable threat intelligence on malware.
YARA Rule Repository and Investigation Workbench: Consolidated threat detection rulesets for use in optimizing detection and threat hunting. Threats can be hunted retrospectively by applying YARA rulesets through all embedded content for tagging and identifying indicators of interest.
Connectors and Threat Tool Integrations: Technology and workflow integrations facilitate the collection, analysis and enrichments of files and indicators from a wide array of sources. A rIch set of APIs provide enriched intelligence back to various systems.