Trends, threats and techniques that comprised the 2021 threat landscape
Ransomware dominated the threat landscape in 2021, with groups adopting new techniques such as double extortion and “as-a-service” models to evade detection and maximize their earnings, a Red Canary report reveals.
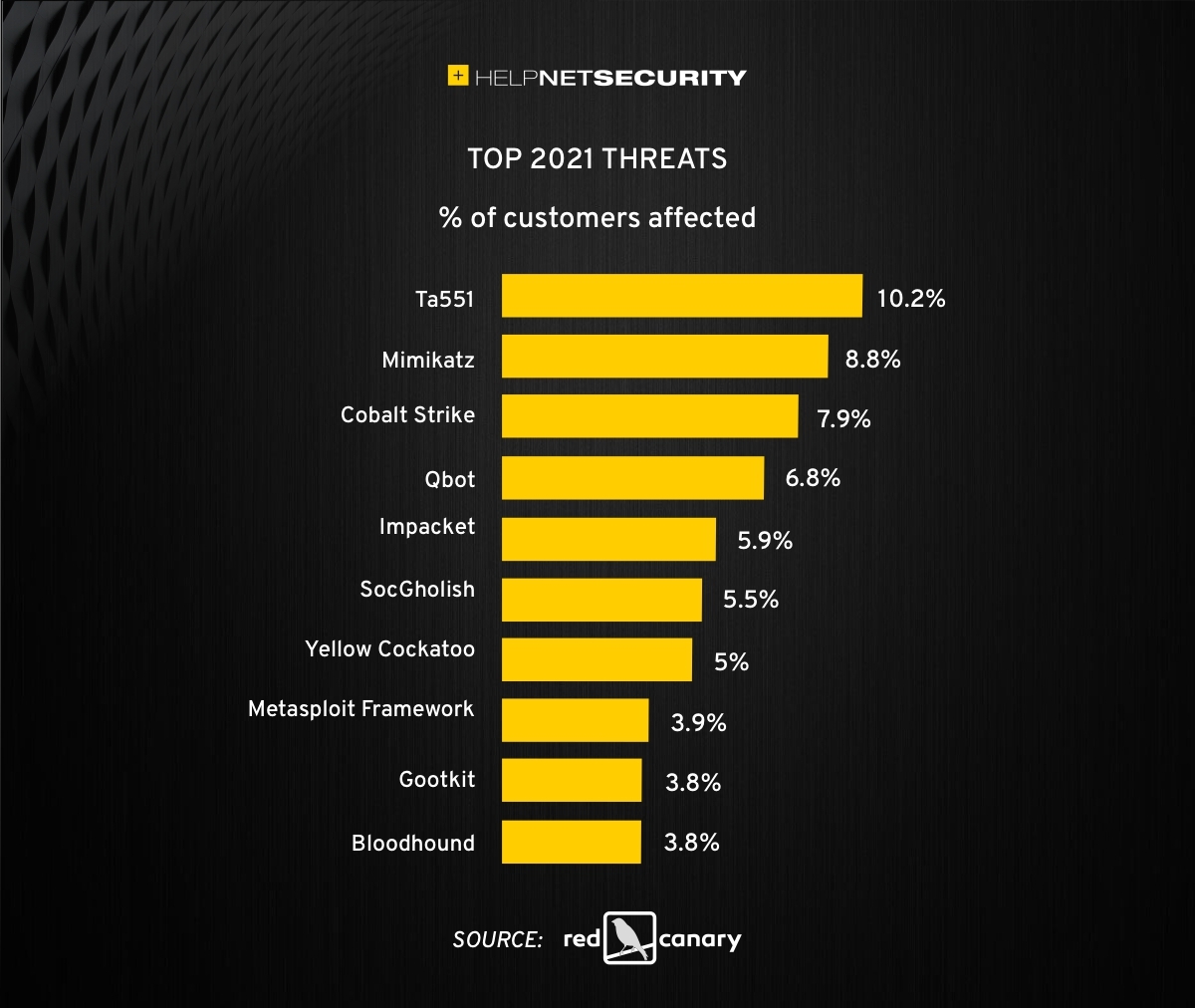
The report explores the top 10 threats impacting the majority of Red Canary customers – from adversary favorites like Cobalt Strike to new activity clusters like Rose Flamingo – and the most common techniques that adversaries use to carry out these attacks, including guidance for companies to strengthen their ability to detect these threats.
“These threats are less sensational than you might find elsewhere, but they’re the ones that will impact the majority of organizations,” said Keith McCammon at Red Canary. “This report addresses highly prevalent threats and the tried-and-true techniques that are wreaking havoc on organizations.”
Legitimate tools are being used for nefarious purposes
Adversaries have continued to carry out attacks using legitimate tools. As security tools increase in sophistication, adversaries are finding it more difficult to develop and deploy their own malware that evades defenses. As a result, adversaries rely on administrative tools — like remote management software — and native operating system utilities out of necessity, co-opting tools that are guaranteed or likely to be installed on a device rather than introducing non-native software.
Several of the top 10 threats and techniques highlighted in the report are used by adversaries and administrators or security teams alike, including command and control (C2) tool Cobalt Strike, testing tool Impacket, and open source tool Bloodhound. Cobalt Strike, in particular, has never been more popular, impacting 8% of Red Canary’s customers in 2021. Some of the most notorious ransomware operators, including Conti, Ryuk and REvil, are known to rely heavily on Cobalt Strike.
Coming in at the No. 5 ranking, Impacket is a collection of Python libraries that is used legitimately for testing but is abused by ransomware operators. This is another favorite among adversaries, as it’s known to evade detection due to its difficulty to be differentiated as malicious or benign.
Ransomware dominated the threat landscape
Ransomware was top billing for some of last year’s most destructive cyberattacks. The report describes the new tactics that ransomware groups used in 2021, such as double extortion, which applies pressure to victims in more than one way to coerce them to pay a ransom.
Last year also brought the rise of the affiliate model, which made tracking malicious activity more difficult because intrusions can often result from an array of different affiliates providing access to different ransomware groups. Examples of this include the Bazar and Qbot trojans, used by adversaries to gain initial access into environments before passing off access to ransomware or other threat groups.
The report analyzes several new ransomware families that became more prevalent in 2021, including BlackByte, Grief, Hive, Yanluowang, Vice Society and CryptoLocker/Phoenix Locker, while also taking a look at the families that tapered off, like Egregor, REvil, BlackMatter and Doppelpaymer. Many of the emergent ransomware families were similar to those that became less or inactive, leading analysts to assess that known adversaries resurfaced using a new name.
The “as-a-service” model became the norm
The threat landscape moved toward a Software-as-a-Service (SaaS) economy in 2021, muddying the already murky waters of attribution. While Ransomware-as-a-Service (RaaS) has been widely reported for years, this model has now become the norm for adversaries. While Red Canary has been tracking some “as-a-service” models like TA551 over the years, others are just now coming into focus. In particular, Red Canary tracks multiple phishing affiliates that dropped variants of the Bazar family of malware.
This economic model lowers the technical barrier to entry, allowing operators to purchase capabilities rather than develop them. Between Phishing-as-a-Service, Access-as-a-Service, and Crypters-as-a-Service, it has never been easier to find an adversary for hire.