More organizations are paying the ransom. Why?
Most organizations (71%) have been hit by ransomware in 2021, and most of those (63%) opted for paying the requested ransom, the 2022 Cyberthreat Defense Report (CDR) by the CyberEdge Group has shown.
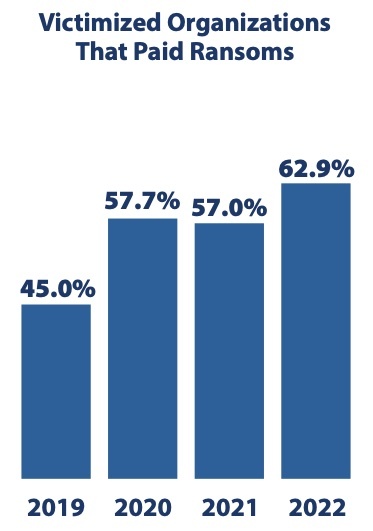
The research company says that possible explanations for the steady yearly rise of the percentage of organizations that decided to pay the ransom may include: the threat of exposing exfiltrated data, increased confidence for data recovery, and the fact that many organizations find that paying a ransom is significantly less costly than system downtime, customer disruption, and potential lawsuits.
“72% of ransom-paying victims recovered their data [in 2021], up from 49% in 2017. This increased confidence for successful data recovery is often factored into the ransom-paying decision,” the company noted.
Similarly, BakerHostatler’s 2022 Data Security Incident Response Report says that in ransomware incidents the US-based law firm was called in to manage in 2021, ransomware groups provided decryptors and stuck to their promise to not publish stolen data 97% of the time.
“Ransomware gangs have noted that when they are conscientious about helping victims recover their data, other victims are more likely to pay ransoms, which increases the profits of the gangs and creates a greater incentive to launch more campaigns,” CyberEdge Group noted.
Longer negotiations lead to smaller payments
“The most frequent client requests this year included assistance with the ransom ‘pay-no pay’ decision tree, OFAC compliance, and ransomware playbooks,” Ted Kobus, Chair of the Digital Assets and Data Management Group at BakerHostetler, shared.
Recent numbers provided by Palo Alto Networks and Coveware show that the average amount organizations pay to get their data back has risen considerably: Coveware says $322,168 (in Q4 2021) and PAN says $541,010 (in all of 2021, for cases worked by its Unit 42 consultants).
BakerHostatler’s report, which is based on the incidents the law firm handled in 2021, shows a similar picture, but says that the average ransom demand paid in 2021 ($511,957) is roughly two-thirds the average amount paid in 2020 – i.e., that it has decreased.
“Over the same time period, the median time between demand and payment was eight days compared to five days in 2020. This is likely a driving factor in the decrease in the average ransom demand paid,” the US-based law firm pointed out.
“More organizations have invested in improving their data backup capabilities and are able to continue at least partial operations after a ransomware incident, which puts them in a better position to negotiate for a longer period of time and reach a greater discount for the ransom demand, if the need to pay arises. Also, if a decryptor tool is not needed and an organization is only paying to prevent further disclosure of their data, they can often take more time to negotiate the demand, which can lead to a deeper discount. Developing business continuity protocols and identifying workarounds for critical business operations — prior to an incident — are key to placing organizations in the strongest position if they experience a ransomware incident.”

BakerHostatler’s report also says that:
- Ransomware represented 37% of the matters they handled in 2021 (compared to 27% in 2020)
- Data exfiltration is the “new normal” for ransomware attacks.
- Companies have improved their ability to restore from backups
- Payments for a decryptor are more expensive than only paying to prevent disclosure.