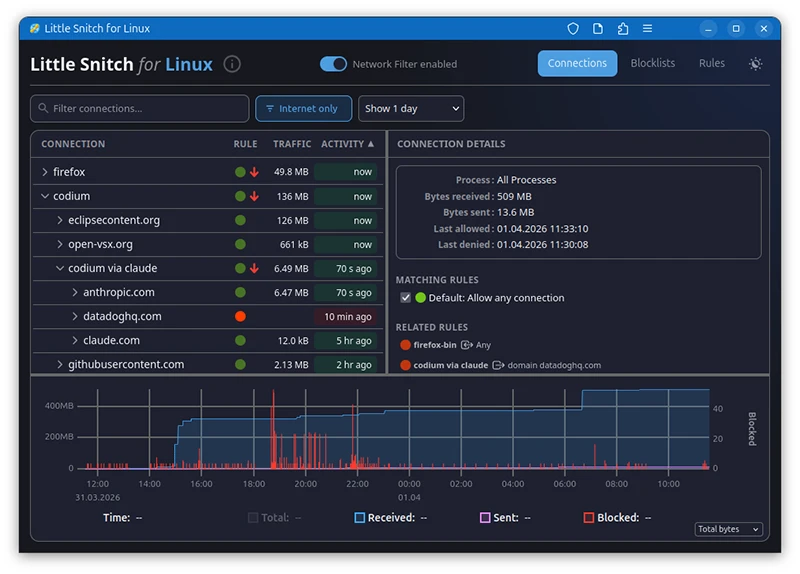
Little Snitch for Linux shows what your apps are connecting to
Network monitoring on Linux has long been a gap for users who want per-process visibility into outbound connections. Existing tools either operate at the command line or were designed for server security rather than desktop privacy. Objective Development, the Austrian company behind the macOS firewall utility Little Snitch, released a Linux version of the tool. It is free and, according to the company, will remain so.
Architecture choices
The kernel component uses eBPF for traffic interception. eBPF operates at the kernel level and offers greater portability than kernel extensions. The main backend is written in Rust. The user interface is a web application, which means a Linux server running Little Snitch can be monitored remotely from any device, including a Mac. The company lists server applications such as Nextcloud, Home Assistant, and Zammad as practical use cases for this capability.
The kernel component and the UI are open source. The kernel code is released so users can review its implementation, fix bugs, or adapt it to different kernel versions. The UI is licensed under GPL v2. The backend, which manages rules, block lists, and the connection view hierarchy, is free to use but closed source.
Feature scope and security limits
“From a feature perspective, Little Snitch for Linux sits somewhere between Little Snitch Mini and the full Little Snitch: functional and useful, but without all the polish and depth of the macOS version. Think of it as an honest first version,” the company said.
eBPF operates under resource constraints that make it possible to bypass the firewall, for example by flooding its tables. The tool is designed to show users what legitimate software is connecting to and to block those connections where desired. It is not designed to stop software that is actively attempting to evade it.
Compatibility
The release is confirmed to work on kernel 6.12 and above. On older kernels, the tool currently hits the eBPF verifier’s maximum instruction limit. The company states that compatibility down to kernel 5.17, where the bpf_loop() function was introduced, is theoretically achievable. Kernel 5.17 compatibility would extend support to Debian 12 (Bookworm) and Ubuntu 24.04 LTS (Noble). The company is inviting contributions from developers with the expertise to close that gap.
Little Snitch for Linux is available on GitHub.

Must read:
- 40 open-source tools redefining how security teams secure the stack
- Firmware scanning time, cost, and where teams run EMBA

Subscribe to the Help Net Security ad-free monthly newsletter to stay informed on the essential open-source cybersecurity tools. Subscribe here!
