
AI traffic is getting bigger, louder, and less predictable
AI workflows need storage that supports repeated movement across the model lifecycle. Large datasets are ingested, transformed, exported for training, pulled back for …

ICS intrusion detection has blind spots that complicate plant security
Industrial control systems on plant floors run alongside a growing layer of monitoring software meant to catch intruders before they reach a turbine, a valve, or a chemical …

A single platform powers SIM farm proxy networks across 17 countries
Racks of phones and 4G modems, connected to carrier networks and rented out as commercial mobile proxy services, are operating across at least 94 locations in 17 countries. An …

Little Snitch for Linux shows what your apps are connecting to
Network monitoring on Linux has long been a gap for users who want per-process visibility into outbound connections. Existing tools either operate at the command line or were …

Residential proxies make a mockery of IP-based defenses
Attack traffic moved through ordinary home and mobile connections in ways that limited the usefulness of IP reputation on its own. GreyNoise observed 4 billion malicious …
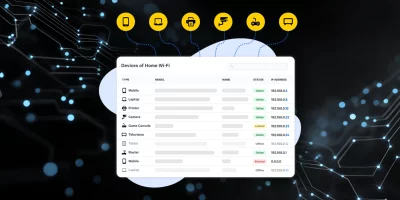
Product showcase: Fing Desktop puts network visibility on your screen
Phones, laptops, smart TVs, cameras, and smart home equipment all use the same network. Knowing what’s connected helps users manage performance and security. Fing Desktop …

Western governments lay the groundwork for secure 6G networks
Governments are preparing for 6G, the next generation of mobile networks, placing security and resilience among their top priorities. In response, seven countries …

Public mobile networks are being weaponized for combat drone operations
On June 1, 2025, Ukraine launched a coordinated drone strike on five airfields inside Russia, disabling or destroying aircrafts. The attack involved more than 100 drones …

CISA orders US federal agencies to replace unsupported edge devices
The US Cybersecurity and Infrastructure Security Agency (CISA) issued a new binding operational directive aimed at reducing a long-standing cyber risk across federal networks: …

pfSense: Open-source firewall and routing platform
Firewalls, VPN access, and traffic rules need steady attention, often with limited budgets and staff. In that context, the open source pfSense Community Edition (CE) continues …

Wi-Fi evolution tightens focus on access control
Wi-Fi networks are taking on heavier workloads, more devices, and higher expectations from users who assume constant access everywhere. A new Wireless Broadband Alliance …

Formal proofs expose long standing cracks in DNSSEC
DNSSEC is meant to stop attackers from tampering with DNS answers. It signs records so resolvers can verify that data is authentic and unchanged. Many security teams assume …
Featured news
Resources
Don't miss
- Microsoft May 2026 Patch Tuesday: Many fixes, but no zero-days
- Stealthy hackers exploit cPanel flaw in active backdoor campaign (CVE-2026-41940)
- Amazon Quick authorization bypass let users reach blocked AI chat agents
- Download: The IT and security field guide to AI adoption
- JetBrains TeamCity vulnerability allows privilege escalation, API exposure (CVE-2026-44413)