The exploit gap is closing, and your patch cycle wasn’t built for this
The Cloud Security Alliance has published a briefing on what it calls a turning point in the threat landscape: the time between a vulnerability being discovered and a working exploit is shrinking fast.
The briefing centers on Anthropic’s Claude Mythos, which autonomously found thousands of zero-day vulnerabilities across major operating systems and browsers, generated working exploits without human guidance, and achieved significant exploit success rate in internal testing.
Asymmetry in offense and defense
The structural problem is asymmetry. AI lowers the cost and skill requirement for finding and exploiting vulnerabilities. Defenders still operate patch cycles, risk models, and detection systems built for human-speed threats. Those systems were not designed for an environment where the average time-to-exploit, based on data from Sergej Epp’s Zero Day Clock, now sits under 20 hours. (For more context about this data, and why it might not be as relevant, I suggest you read Anthony Jones’ LinkedIn post.)
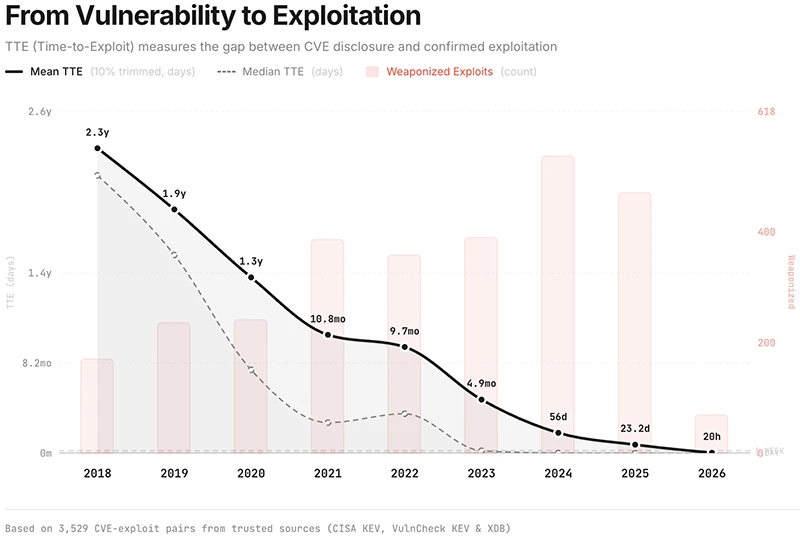
At the moment, the average time-to-exploit data sits under 20 hours (Source: Zero Day Clock)
Offensive AI capability has been escalating since mid-2025. In June of that year, autonomous system XBOW reached the top of HackerOne’s U.S. leaderboard. In August, Google’s Big Sleep found 20 real-world zero-days in open source projects. In November, Anthropic disclosed that a Chinese state-sponsored group had used Claude Code to run full attack chains across roughly 30 global targets. By February 2026, Anthropic reported more than 500 high-severity vulnerabilities in open-source software using Claude Opus 4.6. AISLE found 12 OpenSSL zero-days in the same period, including a CVSS 9.8 flaw dating to 1998.
Recommendations for CISOs
Priority actions are organized across immediate, 45-day, and 90-day horizons. They include deploying LLM-based security review into CI/CD pipelines, formalizing AI agent use across all security functions, preparing for a surge in simultaneous patches, and updating risk models built on pre-AI assumptions about exploit timelines.
AI agent adoption is treated as an operational requirement. Optional programs have not overcome cultural resistance, and teams operating without agents cannot match the speed of AI-augmented attacks.
Rich Mogull, Chief Analyst at the Cloud Security Alliance and one of the briefing’s authors, addressed the resistance organizations will encounter: “One of the biggest issues is lack of clarity and direction. To be successful you ideally need to have approved providers and use cases, with enterprise level subscriptions (for governance and cost management), and then provide training on how and where to use them.”
Mogull told Help Net Security that skepticism among practitioners often stems from early poor experiences with less capable models, and that demonstration is more effective than argument.
On the budget and headcount question, Phil Venables, Partner at Ballistic Ventures and former CISO at Google Cloud, pointed to systemic improvement needs across the software development and infrastructure lifecycle:
“CISO teams, but more importantly infrastructure, development and other teams will need to improve their software and IT management tooling to respond to the need for faster vulnerability remediation.”
Venables framed the current period as a forcing function for longer-term changes that organizations already had business reasons to make. “In the medium to long term this reinforces the need to keep an environment continuously up to date, something that organizations need to do for a whole host of other commercial reasons.”
Mogull put the risk of inaction in historical terms: “We have examples of major patch cycles that strained our ability to respond. These include the Kaminsky DNS vulnerability years ago, or Log4j more recently, and a handful of others. Glasswing likely means we could be facing multiple Log4j level events every month. Maybe multiple a week, we just don’t know yet.”
Burnout as an operational risk
The volume of vulnerability disclosures expected in the near term will exceed anything security teams have encountered. The recommendation is to request additional headcount and budget for reserve capacity before automation is in place, and to treat staff resilience as a strategic priority on par with technical controls.
Security teams are absorbing higher vulnerability volume, more code shipped by AI-assisted development, and a larger attack surface simultaneously. Burnout and attrition represent direct operational risk because the expertise needed to navigate this period is scarce and takes years to develop.
The basic controls still matter
Established security practices remain high-priority actions alongside AI tooling. Network segmentation, egress filtering, phishing-resistant MFA, Identity and Access Management, and patch management for known vulnerabilities all raise the cost of attack. Egress filtering specifically blocked every public Log4j exploit.
Longer-term, the briefing calls for a dedicated Vulnerability Operations function, modeled on DevOps practices, staffed and automated for continuous autonomous vulnerability discovery and remediation across an organization’s entire software estate.

Guide: Breach and Attack Simulation & Automated Penetration Testing