machine learning

6G network design puts AI at the center of spectrum, routing, and fault management
Wireless network operators are preparing for a generation of infrastructure where AI is built into the architecture from the start. Sixth-generation networks, expected to …

Malware detectors trained on one dataset often stumble on another
Machine learning models built to catch malware on Windows systems are typically evaluated on data that closely resembles their training set. In practice, the malware arriving …

AI got it wrong with high confidence. Now what?
In this Help Net Security interview, Christian Debes, Head of Data Analytics & AI at SPRYFOX, talks about the growing gap between what AI models do and what their …
Security teams are paying more attention to the energy cost of detection
Security teams spend a lot of time explaining why detection systems need more compute. Cloud bills rise, models retrain more often, and new analytics pipelines get added to …
Banks built rules for yesterday’s crime and RegTech is trying to fix that
Criminals are moving money across borders faster, and financial institutions are feeling the squeeze. Compliance teams feel this strain every day as they try to keep up with …

How researchers are teaching AI agents to ask for permission the right way
People are starting to hand more decisions to AI agents, from booking trips to sorting digital files. The idea sounds simple. Tell the agent what you want, then let it work …

New observational auditing framework takes aim at machine learning privacy leaks
Machine learning (ML) privacy concerns continue to surface, as audits show that models can reveal parts of the labels (the user’s choice, expressed preference, or the result …
The privacy panic around machine learning is overblown
We often hear warnings about how machine learning (ML) models may expose sensitive information tied to their training data. The concern is understandable. If a model was …

AI can flag the risk, but only humans can close the loop
In this Help Net Security interview, Dilek Çilingir, Global Forensic & Integrity Services Leader at EY, discusses how AI is transforming third-party assessments and due …

Researchers develop AI system to detect scam websites in search results
Scam websites tied to online shopping, pet sales, and other e-commerce schemes continue to cause millions in losses each year. Security tools can accurately detect fraudulent …

When loading a model means loading an attacker
You probably think twice before downloading a random app or opening an unfamiliar email attachment. But how often do you stop to consider what happens when your team downloads …
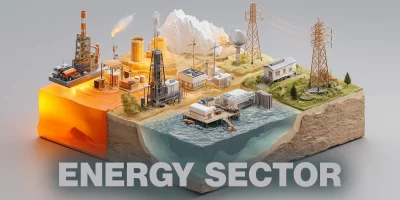
The energy sector is ground zero for global cyber activity
A new study from the Karlsruhe Institute of Technology shows how geopolitical tensions shape cyberattacks on power grids, fuel systems, and other critical infrastructure. How …
Featured news
Resources
Don't miss
- ClickFix campaign delivers Mac malware via fake Apple page
- Poisoned “Office 365” search results lead to stolen paychecks
- What vibe hunting gets right about AI threat hunting, and where it breaks down
- Health insurance lead sites sell personal data within seconds of form submission
- Claude helps researcher dig up decade-old Apache ActiveMQ RCE vulnerability (CVE-2026-34197)