research

GDPR works, but only where someone enforces it
A new measurement study of web tracking across ten countries offers a reality check for anyone working on privacy compliance. Researchers crawled the same set of globally …

Apple Intelligence flaw kept stolen tokens reusable on another device
Apple claims that Apple Intelligence, a GenAI service provided on its operating systems, is designed with an extra focus on user security and privacy through a two-stage …

Researchers build an encrypted routing layer for private AI inference
Organizations in healthcare, finance, and other sensitive industries want to use large AI models without exposing private data to the cloud servers running those models. A …
Workplace stress in 2026 is still worse than before the pandemic
Roughly 40% of employees worldwide said they experienced a lot of stress during the previous day, according to Gallup’s State of the Global Workplace 2026 report, a …
Command integrity breaks in the LLM routing layer
Systems that rely on LLM agents often send requests through intermediary routing services before reaching a model. These routers connect to different providers through a …

Network segmentation projects fail in predictable patterns
Most enterprise networks have segmentation on the roadmap. Many have had it there for years. A survey of 400 U.S.-based network security practitioners who lived through failed …
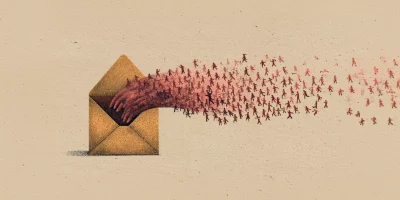
Health insurance lead sites sell personal data within seconds of form submission
Lead generation websites that offer health insurance quotes collect sensitive personal data and sell it to multiple buyers within seconds of a user clicking submit. A study by …

6G network design puts AI at the center of spectrum, routing, and fault management
Wireless network operators are preparing for a generation of infrastructure where AI is built into the architecture from the start. Sixth-generation networks, expected to …

Google study finds LLMs are embedded at every stage of abuse detection
Online platforms are running large language models at every stage of LLM content moderation, from generating training data to auditing their own systems for bias. Researchers …

Which messaging app takes the most limited approach to permissions on Android?
Messaging apps handle sensitive conversations, contacts, and media, and their behavior on a device varies in ways that affect privacy. An analysis of Android versions of …

Tracking drones with the 5G tower down the street
Drone detection in cities is expensive. Dedicated radar installations are cost-prohibitive at scale, cameras have limited range and stop working well at night, and LiDAR …

Malware detectors trained on one dataset often stumble on another
Machine learning models built to catch malware on Windows systems are typically evaluated on data that closely resembles their training set. In practice, the malware arriving …
Featured news
Resources
Don't miss
- OAuth marketplace apps keep access after publishers vanish
- The modern-day business can learn a lot about risk from this year’s mega events
- Spotless compliance evidence can still hide a broken control
- From critical to controlled: Cutting vulnerabilities in a live manufacturing environment
- Attackers already know the secrets are on your developers’ machines. Do you?