software

OpenVPN releases version 2.7.0 with expanded protocol and platform updates
OpenVPN version 2.7.0 is now available. The update advances support for multi-address server configurations and updates client functionality across operating systems. The …

OpenClaw Scanner: Open-source tool detects autonomous AI agents
A new free, open source tool is available to help organizations detect where autonomous AI agents are operating across corporate environments. The OpenClaw Scanner identifies …
Zen-AI-Pentest: Open-source AI-powered penetration testing framework
Zen-AI-Pentest provides an open-source framework for scanning and exercising systems using a combination of autonomous agents and standard security utilities. The project aims …

Allama: Open-source AI security automation
Allama is an open-source security automation platform that lets teams build visual workflows for threat detection and response. It includes integrations with 80+ types of …
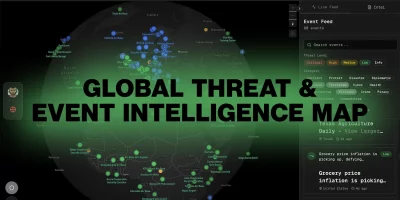
Global Threat Map: Open-source real-time situational awareness platform
Global Threat Map is an open-source project offering security teams a live view of reported cyber activity across the globe, pulling together open data feeds into a single …
OpenAI releases Codex macOS app for agent-based software development
OpenAI has launched the new Codex app for macOS, a dedicated workspace for managing multiple AI coding agents in parallel. The app is designed to help developers reduce …
Product showcase: 2FAS Auth – Free, open-source 2FA for iOS
Online accounts usually rely on a password, but passwords alone can be weak if they’re reused, easily guessed, or stolen. Two-factor authentication (2FA) adds a second layer …

Open-source AI pentesting tools are getting uncomfortably good
AI has come a long way in the pentesting world. We are now seeing open-source tools that can genuinely mimic how a human tester works, not just fire off scans. I dug into …
Pompelmi: Open-source secure file upload scanning for Node.js
Software teams building services in JavaScript are adding more layers of defense to handle untrusted file uploads. An open-source project called Pompelmi aims to insert …

Hottest cybersecurity open-source tools of the month: January 2026
This month’s roundup features exceptional open-source cybersecurity tools that are gaining attention for strengthening security across various environments. OpenAEV: …

OPNsense 26.1 brings updates to open-source firewall management
OPNsense, the open-source firewall and network security platform, reached version 26.1, adding a range of updates affecting management, traffic visibility, automation …
CERT UEFI Parser: Open-source tool exposes UEFI architecture to uncover vulnerabilities
CERT UEFI Parser, a new open-source security analysis tool from the CERT Coordination Center has been released to help researchers and defenders examine the structure of …