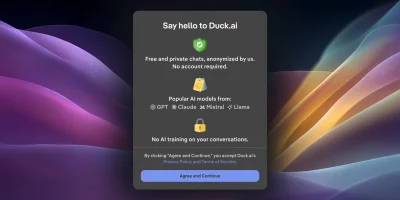
DuckDuckGo enables AI voice chat without saving voice data
DuckDuckGo has added voice chat to Duck.ai, allowing users to speak to an AI assistant while keeping audio private, unrecorded, and excluded from AI training. Voice chat is …

How AI is reshaping attack path analysis
Cybersecurity teams are overwhelmed with data and short on clarity, while adversaries use AI to move faster and operate at unprecedented scale. Most organizations collect …

Face scans and ID checks are coming to Discord
Discord users will soon see a change to how their accounts work. From early March 2026, access to some features will require age verification using an ID or a face scan. The …

What happens when cybersecurity knowledge walks out the door
In this Help Net Security interview, Andrew Northern, Principal Security Researcher at Censys, explains why mentorship matters and what organizations risk losing when senior …

AI-driven scams are eroding trust in calls, messages, and meetings
In this Help Net Security video, Miguel Fornés, Governance and Compliance Manager at Surfshark, discusses how AI is changing social engineering attacks. He describes how tasks …

Cybersecurity jobs available right now: February 10, 2026
Cloud Security Engineer KPMG | Israel | On-site – No longer accepting applications As a Cloud Security Engineer, you will establish, secure, and support critical Azure …

Ransomware group breached SmarterTools via flaw in its SmarterMail deployment
SmarterTools, the company behind the popular Microsoft Exchange alternative SmarterMail, has been breached by a ransomware-wielding group that leveraged a recently fixed …

European Commission hit by cyberattackers targeting mobile management platform
The European Commission’s mobile device management platform was hacked but the incident was swiftly contained and no compromise of mobile devices was detected, …

EU targets Meta over WhatsApp AI access restrictions
The European Commission believes Meta breached EU competition rules by blocking other AI assistants from accessing and interacting with users on WhatsApp. The case centers on …

BeyondTrust fixes easy-to-exploit pre-auth RCE vulnerability in remote access tools (CVE-2026-1731)
BeyondTrust fixed a critical remote code execution vulnerability (CVE-2026-1731) in its Remote Support (RS) and Privileged Remote Access (PRA) solutions and is urging …
Linux kernel 6.19 reaches stable release, kernel 7.0 work is already underway
Development activity on the Linux kernel continues into early 2026 with the stable release of version 6.19. Kernel maintainers have completed the pre-release cycle and merged …

OpenAI updates Europe privacy policy, adding new data categories
OpenAI has updated its Europe-facing privacy policy following the November 2024 EU revision, clarifying scope, expanding coverage, and detailing user controls. The updated …