New Quicktime Player security problems
Security researcher Luigi Auriemma found a new remote buffer overflow in Quicktime Player.
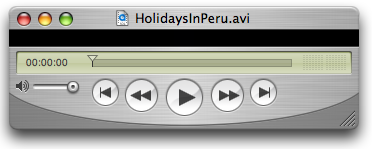
The buffer-overflow happens during the handling of the HTTP error message and its visualization in the LCD-like screen which contains info about the status of the connection.
The copying instruction is visible starting at offset 0x6761d559, the return address can be overwritten completely by the 4 bytes at offset 1926 of the error message, only NULL and carriage-return/line-feed chars are not allowed to use and after the exploitation EAX will point to the same offset where is located the data which overwrote the return address (so EAX + 4 points to the shellcode).
For exploiting this vulnerability needs only that a user follows a rtsp:// link. If the server’s port 554 is closed, Quicktime will automatically change the transport and will try the HTTP protocol on port 80. The 404 error message of the server (other error numbers are valid too) will be visualized in the LCD-like screen.