Vulnerability in TimThumb WordPress plugins: The effects
With the popularity of the WordPress blogging platform, security researchers here at Websense Security Labs are sure to sit up and take note of any reported zero-day threats affecting the platform itself or the plugins used by blog masters.
Recently, we saw a post by Mark Maunder of technology company, Feedjit, where he noticed a compromise occurring due to a WordPress plugin. The danger was this was a zero-day issue affecting a popular image re-sizing tool often used within WordPress. That was on August 1.
Sure enough, just one week after this initial warning, our ThreatSeeker Network began to see code injected into WordPress Web sites. At first we saw the injected domain name hxxp://superpuperdomain.com/ injected at the foot of compromised WordPress blogs. This code appears to have been delivering advertisements to end users via redirects to search engines.
Last Friday, we saw a slight adaptation within the injected code. This time, browsers to compromised sites led to the domain hxxp://superpuperdomain2.com/, which seemingly was a placeholder for more nefarious malicious activity. Websense customers are protected with our Advanced Classification Engine.
Interestingly, over the weekend, we saw the number of injections leading to the first URL decrease as the use of the second URL ramped up on August 12, as the chart below shows:
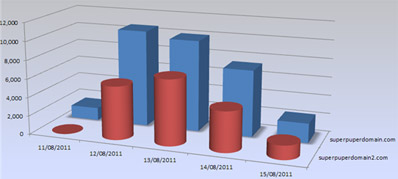
This course of events is fairly typical in the life of a zero-day vulnerability. As the issue becomes known, developers rush to fix the vulnerability. In the meantime, malware authors seek to launch attacks on vulnerable websites and deliver variations of attack code to bypass security products. In this case, we saw peaks of 10,000 WordPress-running Web sites infected with the code.
If you are running WordPress on your blog and want to find out more about TimThumb and how to get the latest version, you should take a look at the TimThumb Project page.

Author: Carl Leonard, Websense Security Labs blog.