Ransomware impersonating European police agencies
Ransomware has been around for quite some time and likely won’t disappear soon, as it usually does manage to make inexperienced users fork over to the criminals quite a considerable amount of money in one go.
Users of a number of European countries have lately been targeted with localized social engineering tactics in order to first download the offending malware and then to pay up to make their computers “unblocked”.
Usually distributed via drive-by downloads when the user lands on a page hosting the Exploit kit, the ransomware is downloaded and executed automatically and the users are presented with a warning message seemingly coming from the main law enforcement agency in their country:
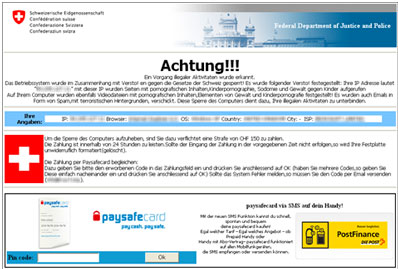
According to Microsoft, these warnings currently impersonate the The German Federal Police, GEMA (Germany’s performance rights organization), the Swiss “Federal Department of Justice and Police”, the UK “Metropolitan Police”, the Spanish Police and the Dutch Police.
The message these warnings contain is always the same – “Attention! Illegal activity was detected. The operating system was locked for infringement against the laws of [name of the country]. Your IP address is [the user’s IP address, as provided by the geolocation service the malware queries].”
It then proceeds to accuse the users of many illegal activities and asks them to pay a fine via Paysafecard or Ukash within 24 hours if they don’t want to have the contents of their hard disks deleted.
The fines in question vary: 50-250 euros for German users, 100 euros for Spanish and Dutch ones, 75 British pounds for Brits, and 100 francs for the Swiss. Microsoft researchers say that the pages hosting the malware are pretty adept at spotting from which country the user is connected to the Internet, so most of the time they are served with the right localized version of the scareware.
“All the localized versions of the ransomware that we’ve encountered so far, except for the more recent GEMA case, have a very similar codebase,” they say. “The HTML front-end has been translated, while the back-end stays almost the same, with the exception of some obfuscation layers. This fact indicates that they were created by the same gang, which has put some effort into designing an easy-to-localize solution.”
They warn users that even if they do pay the requested fine, their action will not resolve their problem. When the user pays the fine, receives a code for it and posts it to the server owned by the perpetrators of the scam, the response is discarded, and the computer remains locked.