Mandiant APT1 report used as a lure in phishing campaigns
Mandiant is warning that two malicious versions of their recently released APT1 report have been detected being used as lures in two distinct email phishing campaigns.
The first has been spotted by Symantec, and comes in an email written in Japanese:
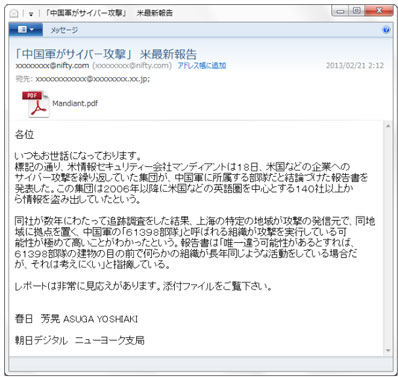
The attached file – Mandiant.pdf – opens a blank PDF and executes exploit code for a recently patched Adobe Acrobat and Reader remote code execution vulnerability.
“From our analysis, the exploit fails to drop any malware onto the computer. It is worth noting that there may potentially be other variants that are successful in dropping malware,” shares Symantec’s Joji Hamada, who also made sure to add that the email has obviously been written by someone who is not a native Japanese speaker.
“Could the Comment Crew [one of the names given to the Chinese hacker group described in the above mentioned Mandiant report] be playing a prank in response to the publication or did someone just make another careless mistake in performing the attack as is the case for so many of these targeted attacks?” he asks, but admits that they don’t know the answer.
The second campaign was revealed by Brandon Dixon, security intelligence engineer at Verisign, in a post on his blog.
He says that the malicious file delivered via email is named Mandiant_APT2_Report.pdf, and once the victims try to open it, they are asked to enter a password in order to peruse it.
“Once executed on the system, a new process under the name ‘AdobeArm.tmp’ was identified running and the original Mandiant APT1 report is shown,” he notes, then says that this same payload was first collected on November 6th, 2012 and is simply being reused without having been changed.
“The PDF itself has a fair bit of JavaScript in it that resembles the CVE-2011-2462 exploit from back in December of 2011. Embedded within the payload is the EXE written to the system, but also a compressed flash file and several JavaScript objects that also contain traces of 2011 code, again showing re-use,” he pointed out.
The dropped malware contacts a domain that has been flagged in many previous attacks against human rights activists in Tibet-themed campaigns.