FastPOS malware exfiltrates data immediately after harvesting it
POS malware might have taken a backseat when ransomware became the go-to malware for many cyber crooks, but stealing payment card information to effect fraudulent transactions is still a lucrative business.
Trend Micro researchers have recently analyzed a new POS malware family sporting some interesting functionalities.
One of these is what made them dub the threat FastPOS: the malware does not wait to collect a batch of data and then send it periodically to the C&C server, but does so each time some of it is harvested. The traffic between the malware and the C&C server is not encrypted.
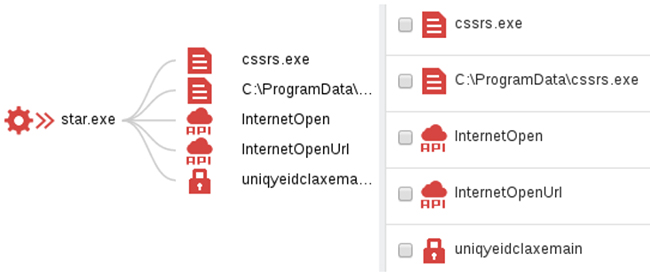
Visual representation of the infection
FastPOS collects both payment card data (scrapes it from the RAM) and keystrokes (via a keylogger thread).
“Keyloggers often go together with PoS threats as the former enable the attackers to do reconnaissance and obtain other information aside from the stolen data from the credit card scrape. Stolen information from keyloggers may also vary between the products or services purchased and the card security code (unique card code/card identification number) being asked in some establishments,” the researchers explained.
“FastPOS implements a simple key-logging functionality similar to another PoS threat, NewPosThings, in that keylogged data are held in memory with no file written in disk. As such, this poses challenges to detection and removal of the malware from PoS systems.”
The RAM scraping process uses a custom algorithm, and the malware is apparently only after data about international cards, unrestricted for authorization, and which don’t require PINs.
FastPOS gets delivered to unsuspecting victims through file sharing services, or through direct file transfer via VNC. If has also been spotted being served for download from a compromised medical website.
In earlier versions it required an administrative account to run, but not anymore.
“Trend Micro has observed infections in SMBs, as well as enterprises. We also surmise that the locations which have FastPOS infections are sometimes the remote offices with open remote VNC access,” the researchers shared.
Infections have been spotted in Taiwan, Japan, Hong Kong, Brazil, France, and the US, in organizations spanning several industries including retail, hospitality, and healthcare.
The malware has been stealing data about payment cards issued by banks in South Korea, Brazil, the UK, Japan, France, Phillipines, and the US.