Healthcare IT professionals are overconfident
A Dimensional Research study evaluated the confidence of IT professionals regarding the efficacy of seven key security controls, which must be in place to quickly detect a cyber attack in progress. Study respondents included 763 IT professionals from various industries, including 101 participants from the healthcare sector.
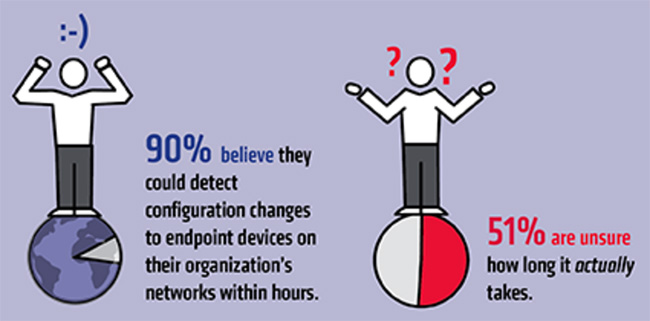
Healthcare IT professionals participating in the study were overconfident in their ability to quickly collect the data needed to identify and remediate a cyber attack. For example, while less than half of the respondents (forty-nine percent) know exactly how long it would take their vulnerability scanning systems to generate an alert if unauthorized devices were detected on their networks, ninety percent believe they would be alerted within hours.
“There’s no argument that these basic controls work and contribute directly to an organization’s cyber security, yet the research shows they are not in place at enough healthcare organizations,” said Tim Erlin, senior director of IT security and risk strategy at Tripwire. “This is occurring at a time when the healthcare industry is facing unique cyber threats, from physical theft to sophisticated ransomware campaigns.”
Additional findings from the study:
- Nearly two-thirds of the respondents (sixty percent) believe their automated tools do not pick up all of the critical details or information that is needed to identify the locations and departments where the unauthorized devices were detected.
- Eighty-three percent of the respondents believe they could detect configuration changes to a network device within hours; however, only fifty-four percent know how long the process would actually take.
- Nearly half of the respondents (forty-five percent) said critical vulnerabilities detected by their scanning tools are not fixed or remediated within 30 days.
- Forty-three percent of the respondents said less than eighty percent of patches succeed in a typical patch cycle.

“The basics of finding unauthorized devices and vulnerabilities and applying patches in a timely manner should be done at every organization in order to create a baseline of cyber security. These fundamental controls should be in place before organizations look at the latest shiny security object,” Erlin concluded.