BankBot Trojan found lurking on Google Play
As predicted earlier this year, the leaking of the source code and instructions for creating a potent Android banking Trojan has resulted in a surge of malware based on it.
Initially, the malware – dubbed BankBot – was being delivered via third-party Android app markets, and targeted mostly Russian users. But now the apps it targets are that of over 400 financial institution around the world (the extensive list can be found here) as well as most of the popular online payment apps such as PayPal.
In addition to this, the crooks behind this malware are repeatedly succeeding in bypassing the protections put up by Google, and making the Trojanized apps available for download on Google Play.
First it was disguised as a legitimate weather forecast application (Good Weather and World Weather).
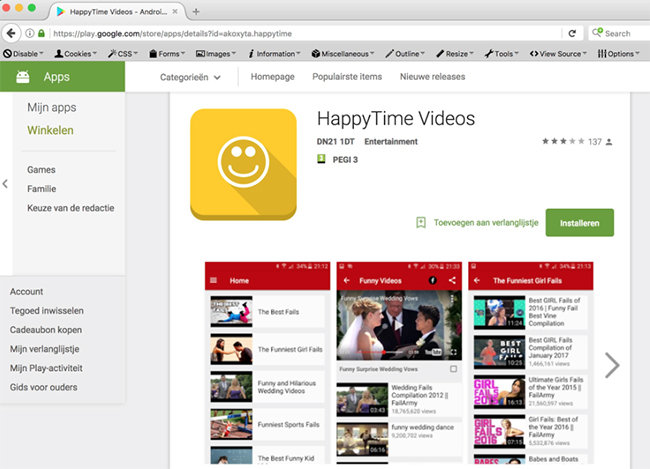
Now, according to Securify, the malware comes bundled in Trojanized versions of video apps – Funny Videos 2017 and Happy Times Videos.
The former was spotted last week, and was uploaded the week before that. Before getting pulled from the store, it was downloaded at least 1,000 times. The latter, flagged on Monday, has also been removed.
Google is becoming better at reacting quickly to reports about apps’ malicious nature, but it would be even better if they detected them themselves and prevented them from being offered for download in the first place.
As Securify researchers noted, “Google Play Store automated security checks needs some serious updating.”
BankBot variants steal online banking and other credentials by popping up fake login windows over legitimate banking and other apps, and can intercept text messages, which helps the crooks bypass two-step verification protections.
The malware also asks for administrator privileges, and this is something that should trigger warning bells for users, because why would a weather or video app need that?
Users are advised to be extremely careful what apps they install on their devices, even if the app comes from Google Play.