Cryptojacking worm compromised over 2,000 Docker hosts
Security researchers have discovered a cryptojacking worm that propagates using containers in the Docker Engine (Community Edition) and has spread to more than 2,000 vulnerable Docker hosts.
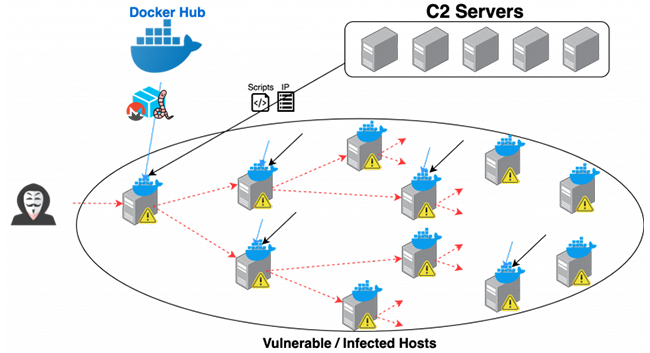
“The attacker compromised an unsecured Docker daemon, ran the malicious Docker container pulled from Docker Hub, downloaded a few scripts and a list of vulnerable hosts from C2 and repeatedly picked the next target to spread the worm,” Palo Alto Networks’s Unit 42 researchers explained.
A worm named Graboid
Dubbed Graboid by the researchers, the worm carries out cryptojacking inside containers, spreads a few host at a time, and mines Monero in short bursts.
“It randomly picks three targets at each iteration. It installs the worm on the first target, stops the miner on the second target, and starts the miner on the third target,” the researchers shared.
“If my host is compromised, the malicious container does not start immediately. Instead, I have to wait until another compromised host picks me and starts my mining process. Other compromised hosts can also randomly stop my mining process. Essentially, the miner on every infected host is randomly controlled by all other infected hosts.”
The reason for this randomized behavior is unknown, but it definitely failed at keeping the cryptojacking unnoticed.
The worm works with a list of 2,034 vulnerable Docker hosts. Some of those have been compromised to also serve as command and control servers from which the malware downloads the shell scripts responsible for:
- Sending the number of available CPUs on the compromised host to the C2
- Downloading a file that contains a list of 2000+ IPs (hosts with unsecured Docker API endpoints), randomly picking one as the next target and pulling and deploying a malicious Docker image (pocosow/centos:7.6.1810) that contains a docker client tool that is used to communicate with other Docker hosts remotely
- Picking one of the compromised hosts from the list and stopping the cryptojacking containers on it
- Picking one of the compromised hosts from the list and pulling and deploying a Docker image (gakeaws/nginx) that contains a cryptojacking binary on the host.
The two malicious Docker images have been downloaded more than 16,500 times, but have since been removed from Docker Hub, along with another cryptojacking image by the same user.
What to do?
The researchers estimated that the malicious actor behind this scheme “owns” a 1,400 node mining cluster that has at least 900 CPU mining power.
Things could be worse for the rightful owners of the compromised hosts, though.
“While this cryptojacking worm doesn’t involve sophisticated tactics, techniques, or procedures, the worm can periodically pull new scripts from the C2s, so it can easily repurpose itself to ransomware or any malware to fully compromise the hosts down the line and shouldn’t be ignored. If a more potent worm is ever created to take a similar infiltration approach, it could cause much greater damage, so it’s imperative for organizations to safeguard their Docker hosts,” they noted.
This means that they have secure Docker daemons exposed to the internet, use secure means of connecting to them, use firewall rules to whitelist incoming traffic to a small set of sources, and consider deploying a security solution that can identify malicious containers.
Another piece of advice is to avoid pulling Docker images from unknown registries or unknown user namespaces. Every so often malicious packages find their way to online repositories/registries, and Docker Hub – the default registry where Docker looks for images – is no exception.