Review: Qualys VMDR
It’s 2020 and the importance of vulnerability management should go without saying. In fact, knowing your assets and performing continuous vulnerability management are two of the Top 20 Critical Security Controls delineated by the Center for Internet Security (CIS).
This is a review of Qualys VMDR (Vulnerability Management, Detection, and Response), an integrated solution for:
- Detecting and identifying your assets
- Vulnerability identification and assessment
- Prioritization of vulnerability remediation efforts
- Finding missing patches and misconfigurations responsible for the vulnerabilities identified
- Patch prioritization and easy deployment of software patches
Qualys VMDR really shines in a hybrid environment of cloud instances (e.g. Amazon AWS EC2s), multiple offices and a remote workforce. Where such a large number of distributed devices is involved, Qualys VMDR minimizes the hassle of tracking those assets and checking what patches and/or mitigations are missing, which pose a high risk to the organization.
To top it off, it’s a cloud-based Software-as-a-Service solution, so it’s one less moving part that must be maintained on site.
Reporting and visualization
If you have thousands of hosts/assets scattered over multiple networks then dashboards, visualization and reporting is how you can easily collect information.
When you first open Qualys VMDR, you’ll be greeted by a default dashboard with pre-defined widgets that you can customize with bar charts, counters and tables. Some scenarios that we tried to display – e.g., visualizing asset breakdowns or vulnerability types – can be easily created, since the user can preview the actual result at the time of creation.
Complex visualizations can also be created, since the queries support Boolean logic and combos like “tags.name:`Cloud Agent` AND software: (name:`CiscoAnyConnect Secure Mobility Client`”. Complex queries are sometimes hard to create, but in Qualys VMDR tooltips, autocomplete and dropdown options are a great help with that.
Specific views into Qualys VMDR’s features, such as seeing which certificates have expired or are about to expire, are presented in a clear tabular view, where sorting by a column works well.
Drilling down into all of your assets – networks, IP addresses, domains, vhosts, asset groups, OSes, apps, ports/services and certificates – is simple, and tables and search bars make it easy to find what you want to see.
Reports based on information from/on scans, maps, patching, authentication, remediation, compliance levels and asset lists can be generated or scheduled for generation. Report templates can be configured. All classic output formats are supported: PDF, HTML, XML, CSV and MHT (Web Archive for Internet Explorer).
The tool has met all our reporting and visualization requirements. But let’s see now is how it handles asset discovery and the application of patches/mitigations.
Asset discovery
Discovery can be performed either with passive scanning sensors, which need to be deployed on-site to monitor the network for information about assets, or by deploying an agent on the machine. Agents work as one would expect, and can be deployed on Windows, deb or rpm-based GNU/Linux distros, and macOS, AIX or BSD. They can either be installed directly on a machine (the user must add his CustomerID to associate the agent with his instance) or they can be deployed over AD or through other provisioning or management processes.
Assets can be organized into asset tags, which work exactly like classic tagging. Hosts can be added either via the manual “select than add” workflow or by simply pasting in a list of IP addresses/ hostnames. Grouping works either on the IP range, DNS, NetBios or Domain level. Per-user grouping and grouping hosts that are detected by a specific scanner are also available options.
One interesting thing we saw here is that each asset group can be labeled according to business impact, function, division and location, which makes searching for organizations’ information assets simpler and easier. Another interesting thing is the ability to add a CVSS metric info to the asset group. This means that a specific group can be labeled with its:
1. Collateral damage potential
2. Target distribution
3. Confidentiality requirement
4. Integrity requirement
5. Availability requirement.
This is useful if we want to add risk-specific information to our assets, which should highly improve the workflow for engineers performing vulnerability management.
Prioritization and remediation
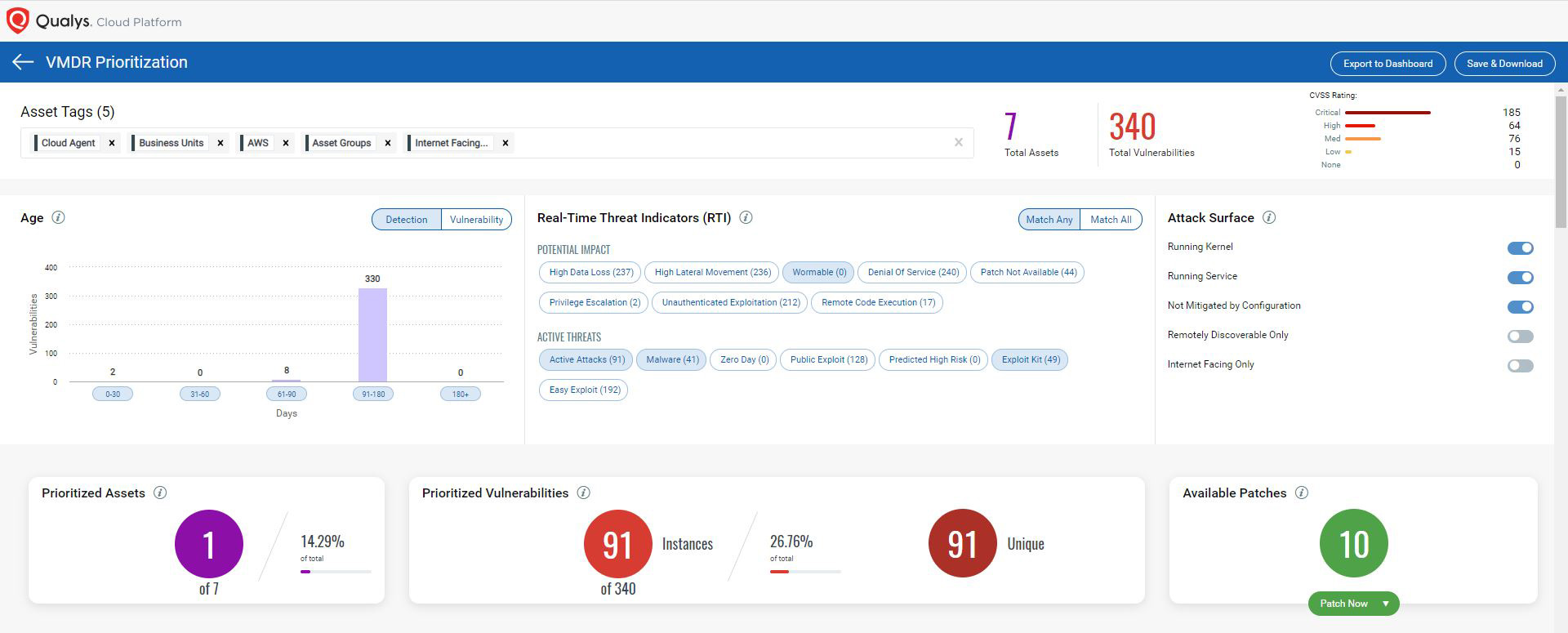
The main view for prioritization is the prioritization report with a dashboard-like interface. This makes sense since, in practice, all of our remediation efforts will be bound in a “view” where we want to work on detection and remediation for a specific group of assets.
The dashboard enables us to select for specific asset tags for the use case in hand, which will then allow us to see the breakdown for the detection age for a number of threat indicators. Threat indicators are also grouped, and can be selected from a number of predefined categories, as seen in the next screenshot.
As an instance, if you want to identify the vulnerabilities getting exploited by malware in workstations then you will select asset tags related to your workstation and choose ‘Malware’ and ‘Wormable’ Threat Intelligence indicator to prioritize the relevant vulnerabilities.
The prioritization report takes a transparent approach to prioritize the vulnerabilities and its remediation efforts, the user has the flexibility to choose the criteria according to the use case in hand.
After we are greeted by the breakdown of our assets/vulnerabilities/patches, we can do our vulnerability management work. We can see what patches/mitigations are missing in our asset groups or we can go over specific assets and see what patches/mitigations are missing from that specific asset.
The recommended patches in the prioritization report take into account the supersedence of the patches and dynamically maps patches to the vulnerabilities to identify the exact patch which will fix the vulnerability(s).
From a workflow perspective, this enables a lot of flexibility and enables both a precise approach and a general/grouped approach. Since our management work won’t be done in one day, reports can be saved so that we can continue where we stopped the day before.
Selecting “Patch now” on the main dashboard will enable us to either create a new patching job, add this set of patches to an existing job, or just view what patches are missing. One part of that workflow can be seen in the following screenshots:
Conclusion and verdict
At the moment, Qualys VMDR doesn’t cover automatic patching for all types of vulnerabilities. It will identify vulnerabilities, but certain mitigations still have to be applied manually (e.g., configuration changes, many GNU/Linux-based patches). Applying software patches is a feature that works for the Windows ecosystem. However, Linux, Mac and Patching using third party patching systems are in the roadmap.
Additional elements such as support for containers and securing containers, mobile device management, and automatic renewal of certificates are scheduled to be released later this year. This is definitely not a deal-breaker, since automation in some of those features is highly dependent on the specific engineering practices inside the organization.
That said, Qualys VMDR successfully solves common enterprise problems: how to perform vulnerability management on a large number of assets, how to identify the assets, and how to find missing patches/misconfigurations and apply mitigations.
For a company that is heavily dependent on the Windows ecosystem and whose assets span to cloud providers and multiple networks, this is an excellent product that resolves a major pain point. It’s Even more important in mixed form environments is the vulnerability management workflow, where identification of missing mitigations is very useful, and Qualys offers an interesting approach for identification.
For existing Qualys customers or those looking to invest in a web scanner or PCI compliance offerings, expanding their tooling with Qualys VMDR makes strategic sense, since it will nicely integrate into the engineering workflow through the Qualys cloud platform.
Qualys has an open training library for VMDR and other tools that can provide our readers with more in-depth information on the inner workings of the product.