Private, unlicensed 5G mobile network adoption may intensify NetOps and SecOps challenges
While 5G sometimes seems like the panacea for just about everything, it will likely intensify the already common friction between NetOps and SecOps teams that will take part in deployments and operations of the 5G mobile network. Besides faster speeds, lower latency, greater coverage and ultra-reliable mobile services across new radio spectrums, 5G brings tectonic changes in mobile architecture and enables totally novel applications with highly complex requirements.
One of the major changes in 5G architecture is the virtualization and network slicing that makes NetOps and SecOps monitoring and control even more challenging. Even the idea of fully understanding a network and all that it includes becomes more difficult and perplexing.
Additionally, a likely surge in the use of IoT devices and mission-critical applications demanding low latency communications adds complexity and complications. These challenges apply to both security and networking. Specifically, the threat surface will be increased as more devices will be connected to more cells.
Just to highlight the tip of the iceberg, we need to consider the fact that some IoT devices likely have lower security capabilities and are even subject to physical security risks as many small cells that will be used indoors and outdoors on lights, signs, storage areas and other infrastructure. Some of these may be cameras, proximity sensors and other kinds of detectors.
As a result, NetOps and SecOps teams will need greater network visibility, assessment tools and security measures. Most of all, teams will need a far greater level of agility to stay ahead of such dynamic changes, both to the network itself, the traffic utilizing it, and the connected elements that can start from machine to machine elements, such as operational technology sensors and controllers, and go far beyond to augmented reality applications.
These new conditions aggravate the traditional networking and security challenges and threaten to intensify the friction between the organizations. 5G standardization has an enhanced security framework over 4G, but there are various new implementations and complexities of design, and NetOps and SecOps teams need to come together to achieve greater agility and accommodate changes and challenges to their new mobile networks more quickly and more efficiently. Today’s means of resolving these differences need to evolve, as teams are already overworked and under-staffed and generally slow in making or accommodating changes to the network.
In new 5G deployments, there will be two options for enterprises:
1. Connect to a public 5G mobile network that’s owned and operated by a mobile operator.
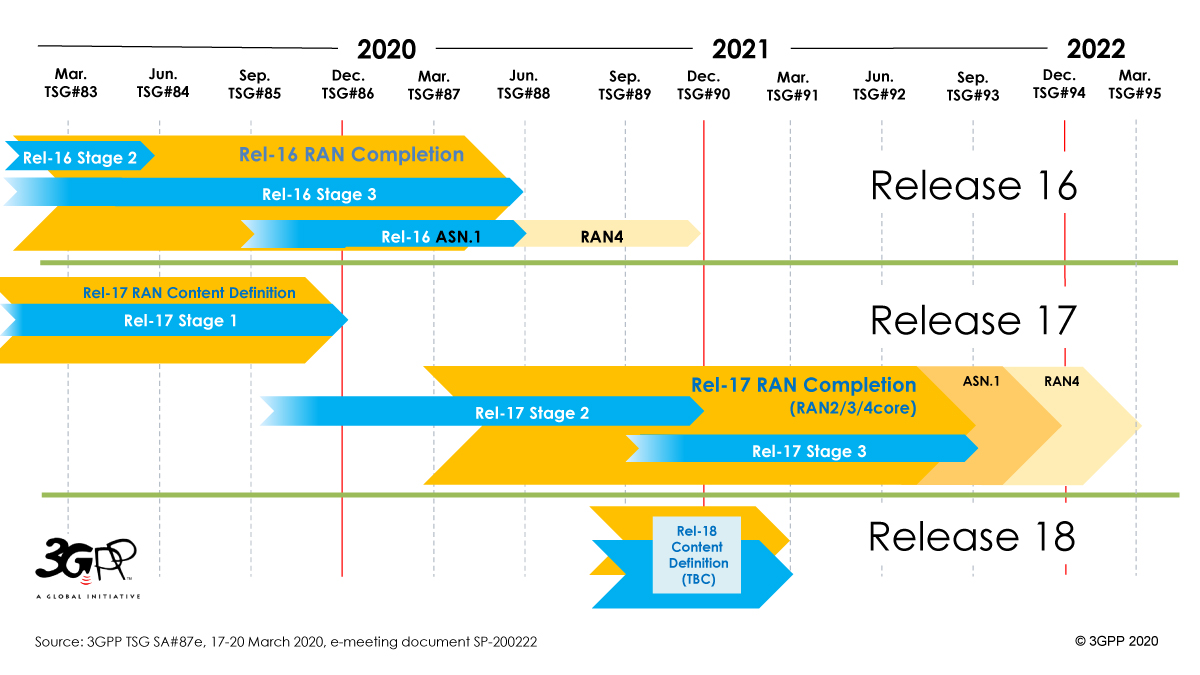
2. Deploy and operate its own private 5G network with non-licensed radio spectrum, known as 3GPP release 16. This is a new standard that will be a new alternative to Wi-Fi and LTE networks with special purpose-build requirements for private industrial networks. This mode can be operated as an outsourced deployment or using a consultancy service or a “build it yourself” model that will probably be more feasible for companies as the technology matures.
Many large industrial and manufacturing enterprises with mega-sites or even multiple sites that will require private mobile interconnections, will select the second option to enable their mobile private communications and reduce dependencies with more control to adapt the mobile network to their business processes and special requirements. Some of the most attractive 5G use cases will justify this trend and will streamline a digital transformation of old industries that are still lagging behind.
Being in control of quality, coverage and operational requirements will drive internal teams to collaborate based on corporate directives and foster security measures on people, processes and connected elements and applications. Organizations putting a premium on security will push enterprises to lean towards private 5G enterprise networks because of the complete segregation it offers. Since 5G slicing that is performed on a public network might share the same physical infrastructure with virtual slices that logically separate customers, sharing the same physical infrastructure by multiple customers will be still a valid concern.
New forms of network virtualization brought by 5G – and specifically private 5G – present new requirements for monitoring, management and security. In particular, the dynamic nature of creating a new slice or segmentation in a mission-critical environment, seemingly out of the blue, or reverting back or changing existing ones calls for constant vigilance. The rise of virtualized computing presented its challenges to security, and new solutions and practices arose to meet them. In much the same way, these virtualized networking practices will create new security challenges and solutions.
5G network slicing is a paramount challenge and operational teams will need to collaborate on having clear procedures that impact both mobile and wireline infrastructure. Additionally, new technology adaption takes time and requires careful planning to inspect various dynamic scenarios that not necessarily known before.
As 5G unlicensed networking will be adapted gradually by the enterprise as a private 5G local area network, it’s hard to know what changes to plan for, so the best planning must be in the form of creating far more streamlined NetOps and SecOps teams that can work together under the same corporate directives to accomplish business objectives and insure top security posture.
This is a new paradigm shift for Enterprise to adopt novel mobile technology and accelerate digital transformation. Organizations will gain new, important capabilities, but they will also be presented with new challenges. Embracing these factors requires evolving from old ways of distancing NetOps and SecOps with opposing roles to more co-team relationships where both can work together more effectively.