2 million malicious emails bypassed secure email gateways in 12 months
Two million malicious emails bypassed traditional email defenses, like secure email gateways, between July 2020-July 2021, according to data from Tessian.
Who’s being targeted and how?
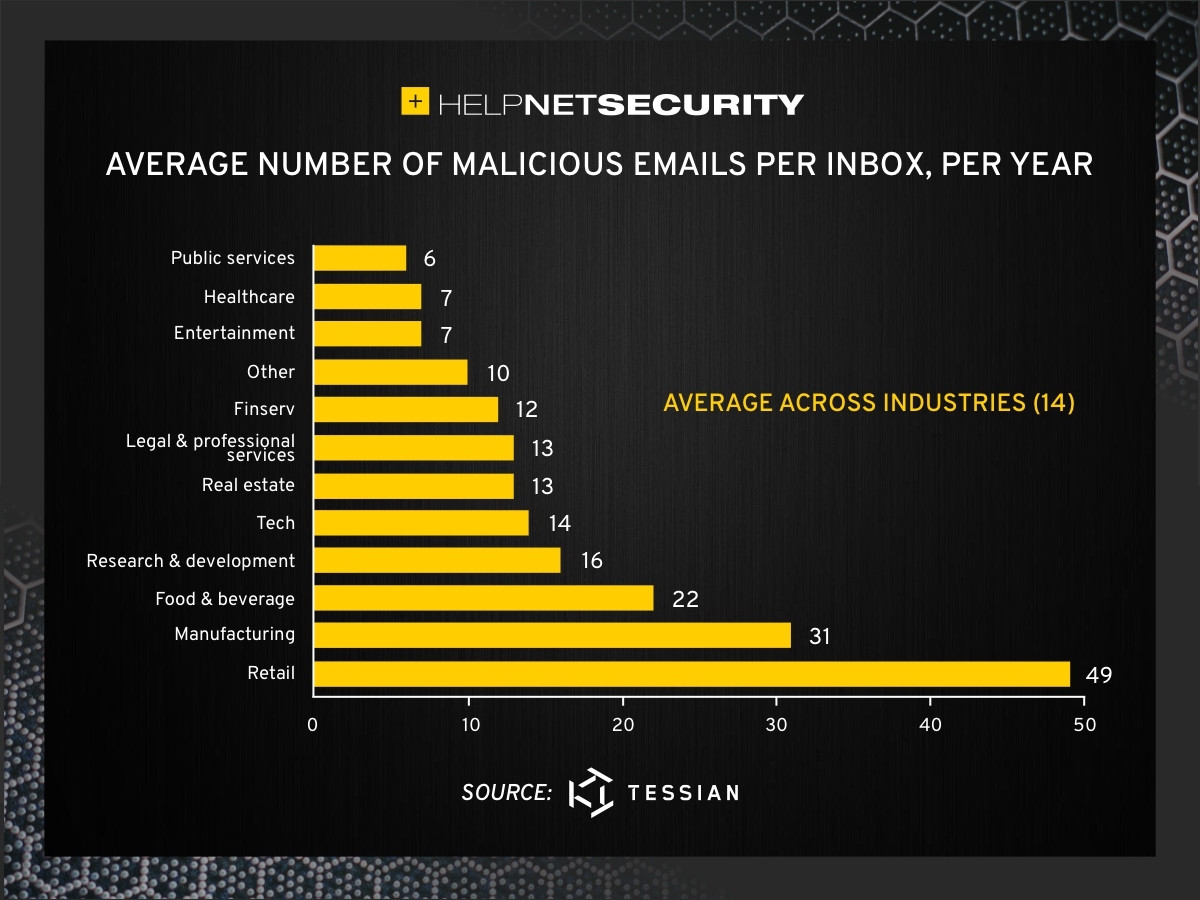
The retail industry was targeted most, with the average employee in this sector receiving 49 malicious emails a year. This is significantly higher than the overall average of 14 emails per user, per year. Employees in the manufacturing industry were also identified as major targets, with the average worker receiving 31 malicious emails a year.
To evade detection and trick employees, attackers used impersonation techniques. The most common tactic was display name spoofing (19%), whereby the attacker changes the sender’s name and disguises themselves as someone the target recognizes. Domain impersonation, whereby the attacker sets up an email address that looks like a legitimate one, was used in 11% of threats detected. These subtle nuances in the email domain aren’t always easy to spot.
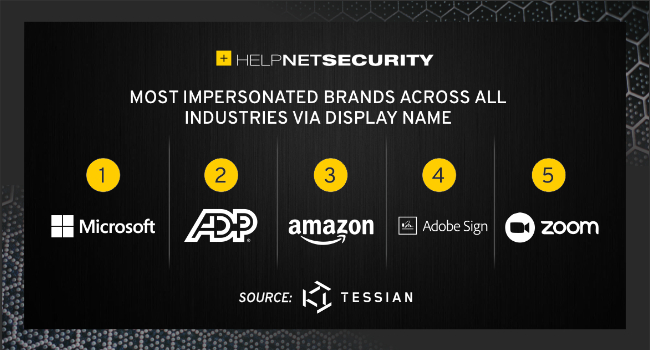
The brands most likely to be impersonated in the emails detected between July 2020 and July 2021 were Microsoft, ADP, Amazon, Adobe Sign and Zoom – the latter likely spurred on by the shift to remote working.
Account takeover attacks were also identified as a major threat, an attack vector that, on average, costs businesses $12,000. In this case, the malicious emails come from a trusted vendor or supplier’s legitimate email address, and likely won’t be flagged by a secure email gateway as suspicious. Data found that account takeover comprised 2% of malicious emails analyzed, and the legal and financial services industries were targeted most by this type of attack.
What’s the motive?
While emails containing attachments were once a popular “spray and pray” method to trick people into downloading malware, 24% of the emails flagged contained an attachment. In addition, 12% of malicious emails contained neither a URL or file – a sign that attackers are moving away from using typical indicators of an attack. Links, however, do still prove to be a popular and effective payload, with 44% of malicious emails containing a URL.
While credential theft is growing in popularity among cybercriminals today, there were more keywords related to “wire transfers” than “credentials”. This suggests that the motive behind these attacks is still largely focused on financial gain.
When are people most vulnerable?
Researchers reveal that most malicious emails are delivered around 2 p.m. and 6 p.m. in the hopes that a phishing email, sent during the late afternoon, will slip past a tired or distracted employee.
Attackers also capitalized on specific times of the year. The biggest spike in malicious emails immediately before and following Black Friday, a time when many people expect to receive a surge of emails touting deals. Attackers can also leverage “too-good-to-be-true” deals, using them as lures in their scams.
“Gone are the days of the bulk spam and phishing attacks, and here to stay is the highly targeted spear phishing email. Why? Because they reap the biggest rewards,” said Josh Yavor, Tessian’s CISO.
“The problem is that these types of attacks are evolving every day. Cybercriminals are always finding ways to bypass detection and reach employees’ inboxes, leaving people as organizations’ last line of defense. It’s completely unreasonable to expect every employee to identify every sophisticated phishing attack and not fall for them. Even with training, people will make mistakes or be tricked.
“Businesses need a more advanced approach to email security to stop the threats that are getting through – the attacks that are causing the most damage – because it’s not enough to rely on your people 100% of the time.”