Bug bounties are broken, and the best security pros are moving on
Penetration testing engagements are organized as scheduled contracts with defined scope, set testing windows, and direct communication channels with client teams. Cobalt’s 2026 Pentester Profile Report describes growing preference for penetration testing as a service (PTaaS) and contract-based testing models.
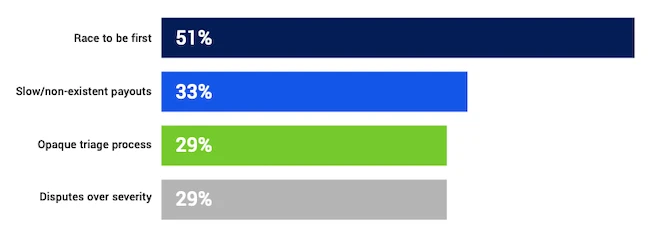
Why pentesters are frustrated with bug bounty (Source: Cobalt)
Many participants prefer contract-based testing over open bug bounty programs and prioritize predictable professional income tied to guaranteed engagements. Pentesting serves as the primary occupation for a large share of this group. Most participants bring years of field experience and describe career goals centered on staying hands-on and maintaining technical standards.
Where testers see the strongest results
Respondents link contract engagements with deeper technical investigations carried out across agreed timelines. This model supports broad test plans, coordinated retesting, and discussion of findings with internal security and engineering teams. Practitioners who participate in both contract work and bug bounty programs attribute most of their highest-severity discoveries to structured engagements.
Reported reasons focus on how the work is organized. Defined scope and dedicated testing time allow extended analysis of attack paths that span multiple systems. Direct access to client stakeholders supports clarification, evidence review, and validation of fixes. Depth of testing and practitioner expertise appear frequently in responses describing this work.
“PTaaS gives us the confidence that our time is valued, but the real advantage is the collaborative nature of PTaaS,” said Jesus Espinoza, Cobalt Core Pentester, IT Security Consultant, and Bounty Hunter. “Unlike bug bounties, we can ask clients questions in real-time to understand their business logic or request specific user roles to test different features. It’s a professional, collaborative environment where we work together to find real vulnerabilities, rather than competing for low-hanging fruit.”
Friction in bounty programs
Bug bounty work follows a different workflow. Participants describe competition to submit simple findings quickly across large researcher pools. Payment delays and uncertainty over rewards surface frequently in responses. Disputes over triage outcomes and vulnerability severity appear as recurring concerns.
Program structure also aligns with certain research patterns. Many say bounty programs lead them toward high volumes of repeatable, lower-level findings. That workflow leaves less room for exploratory testing and complex attack paths that require extended validation and coordinated follow-up.
An experienced technical workforce
The survey group represents an established technical community made up largely of career security testers. Participants commonly report long tenures in security assessment, application testing, and related technical disciplines. Development backgrounds appear frequently, with coding, software building, and tool creation cited as professional interests.
Career stage descriptions reflect senior practitioner profiles with long-term specialization in offensive security testing. Pentesting remains the primary occupation for most participants, reinforcing the profile of a workforce focused on technical execution within defined engagements.
Serious vulnerability discovery forms a routine part of that work. Participants describe identifying previously unknown flaws during professional engagements across enterprise environments. Some report discovering zero-day vulnerabilities. Others describe uncovering unpatched issues that were unknown to vendors at the time of discovery.
Handling of severe findings follows consistent reporting practices described by participants. Many say they stop active exploitation and report critical issues immediately through established client channels. Others describe conducting additional controlled testing to show how multiple weaknesses can combine to create business risk within agreed rules of engagement.
Focus areas for the near term
Participants identify several areas expected to draw security attention in the coming year. Shadow AI systems rank high on that list, alongside identity-related weaknesses and emerging cryptographic concerns. These areas appear frequently in environments where new tooling, complex integrations, and evolving trust models introduce testing challenges.
Human expertise remains central in participant responses. Complex systems are described as requiring contextual understanding, judgment, and coordinated communication that automated tools alone do not provide. That view aligns with preference for engagement models built around sustained collaboration and defined working relationships.
Contract-based testing holds strong support among experienced practitioners seeking sustained technical work and close alignment with client security operations. Open bounty programs continue to serve as an avenue for independent research and opportunistic discovery. Structured engagements receive broader preference across survey measures tied to vulnerability discovery and professional stability within this group.

Download: Blue Report 2025 uncovers how security controls perform in practice