authentication

Proton Pass adds monitored credential sharing for AI agents
Proton Pass, a secure, end-to-end encrypted password manager, added credential sharing through AI access tokens, allowing users to give AI agents access to selected items and …

The new economics of fraud: Cheaper, faster, more convincing
Scams have become one of the fastest-growing consumer risks, driven by AI-enabled impersonation, social engineering, and sophisticated attack methods, according to Visa’s …

7 hard truths security pros should know: 2026 DevOps Threats Report
In 2025, trusted Git hosting platforms became a playground for cyber criminals. This is the main conclusion from the latest “DevOps Threat Unwrapped Report 2026” by …

What happens when your identity provider becomes the kill chain
In this Help Net Security video, Colin Constable, CTO at Atsign, explains why your identity provider (IdP) has become the kill chain in cyberattacks. Attackers steal session …

Earbud sensors can authenticate users by their heartbeat, study finds
Researchers built a continuous authentication system called AccLock that identifies a wearer by the tiny vibrations a heartbeat makes inside the ear canal. The signal comes …
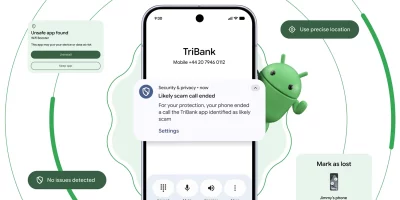
Android pushes new scam, theft, and AI protections in 2026 update wave
Phone scammers spoofing bank caller IDs have driven an estimated $980 million in annual losses worldwide, according to Europol. Android’s 2026 security roadmap takes …

AIMap: Open-source tool finds and tests exposed AI endpoints
Public-facing Ollama servers, MCP endpoints, and inference proxies have multiplied across the internet over the past year, often deployed without authentication or rate …

ChatGPT advanced account security adds passkeys and hardware keys
Journalists, elected officials, researchers, and political dissidents have spent years adapting their accounts to phishing-resistant authentication on consumer platforms. …

FIDO Alliance wants to keep AI agents from going rogue on online payments
AI agents are beginning to shop, log in, and complete tasks with little direct input. That shift is pushing the security industry to rethink how trust works when actions are …

Your IAM was built for humans, AI agents don’t care
Identity and access management was built for a simpler world. One where the hardest problem was a human logging in, and where “Who are you?” was sufficient to …

Users advised to drop passwords and make room for passkeys
In a decisive move that could reshape how users log in online, the National Cyber Security Centre (NCSC) is urging consumers to abandon passwords in favour of passkeys, …

Google brings instant email verification to Android, no OTP needed
Google has introduced cryptographically verified email credentials for Android through the Credential Manager API. This API aligns with the W3C Digital Credential API …
Featured news
Resources
Don't miss
- Dutch police disrupts botnet composed of 17 million devices
- New infostealer reaches enterprise devices through FortiClient EMS vulnerability
- LinkedIn-themed phishing abuses Adobe’s A/B testing platform
- The behavioral signals that sharpen Trojan malware detection
- Zapier exploit chain shows how known anti-patterns compose into critical risk