Android app uses Bluetooth signals to detect nearby smart glasses
Smart glasses with built-in cameras are showing up in more public spaces, and a growing number of people want a way to know when one is nearby. An Android app called Nearby Glasses, developed by Yves Jeanrenaud, attempts to fill that gap by scanning Bluetooth Low Energy traffic for manufacturer identifiers associated with known smart glasses makers.
The project cites several reported incidents that motivated its development, including documented cases of Meta Ray-Ban glasses being used to record people without consent and at least one case where a Harvard student demonstrated real-time facial recognition using the glasses paired with publicly available data.
How detection works
Nearby Glasses does not rely on device names or UUIDs, both of which are inconsistent across BLE advertising frames. It targets the manufacturer-specific data field in BLE advertising packets, specifically the company ID field assigned by the Bluetooth Special Interest Group. These identifiers are standardized, mandatory, and immutable within the BLE spec, which makes them a more stable detection signal than other parts of the advertising frame.
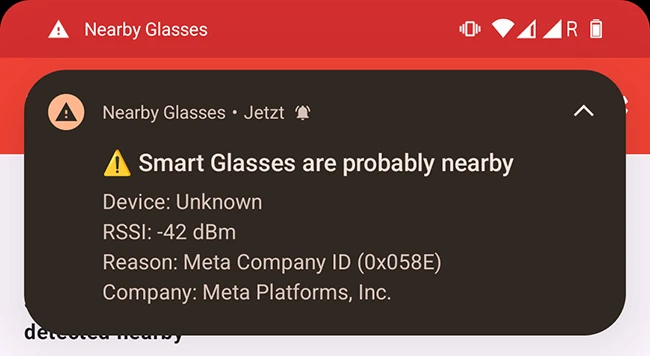
The app currently monitors for four company IDs: 0x01AB for Meta Platforms, 0x058E for Meta Platforms Technologies, 0x0D53 for Luxottica (the manufacturer of Meta Ray-Ban glasses), and 0x03C2 for Snapchat, maker of Snap Spectacles. Users can override the built-in list and enter custom hex values through the settings menu, which lets the app trigger on any manufacturer ID the user specifies.
The app runs as an Android foreground service to maintain scan persistence. When a BLE device matching one of the monitored company IDs is detected at or above a configurable RSSI threshold, the app pushes a local notification. The default threshold is -75 dBm, which corresponds roughly to 10 to 15 meters in open space and 3 to 10 meters indoors.
False positives are a known limitation
Because the detection method targets company IDs shared across an entire manufacturer’s product line, the app will also trigger on other Bluetooth-enabled products from the same companies, including VR headsets. The project documentation acknowledges this openly. Jeanrenaud notes that contextual awareness matters: if there are no VR setups visible nearby, a match is more likely to correspond to wearable glasses.
The notification cooldown is set to 10 seconds by default, which limits alert fatigue while keeping the user informed. RSSI thresholds and cooldown intervals are both adjustable in settings.
Data handling and privacy
The app collects no user data, sends no telemetry, and displays no ads. An optional exportable log records only BLE manufacturer ID codes encountered during a scan session. The log is stored locally and is not transmitted anywhere automatically. The project’s privacy documentation states that installing through Google Play may result in Google collecting install statistics, but the app itself has no data collection functionality.
Detection gaps and roadmap
The project documentation acknowledges that BLE scanning on Android does not always behave predictably. Signal absorption from human bodies, obstacles, and device orientation all affect RSSI readings, which means nearby devices may go undetected in some conditions. The documentation also notes that smart glasses users who intend covert recording typically pair devices in advance, so the pairing-phase device name broadcast, another potential detection vector, is rarely visible in the field.
Jeanrenaud has listed several items for future development. These include expanding the monitored company ID list beyond Meta and Snap, a layout fix for Google Pixel devices where the menu overlaps the status bar, localization support by moving hardcoded text into Android’s strings resource files, and a potential iOS port contingent on access to Apple’s developer toolchain.
A longer-term possibility noted in the project is deeper BLE traffic analysis through packet sniffing, which could reduce false positives by applying heuristics to encrypted transmissions. Jeanrenaud has stated that implementing this would require contributor involvement given the technical depth involved.
The app is available on Google Play and as a direct APK download from GitHub. The source code is written in Kotlin and is publicly accessible in the project repository.