GopherWhisper APT group hides command and control traffic in Slack and Discord
Attackers continue to lean on everyday collaboration platforms to hide command and control traffic inside normal enterprise noise. A newly identified China-aligned APT group pushes that trend further, running its operations through Slack workspaces, Discord servers, Outlook drafts, and the file.io sharing service.
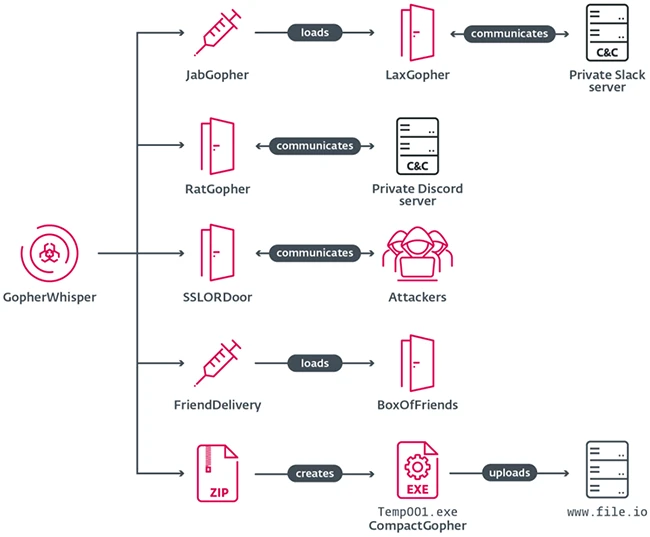
GopherWhisper toolset overview
ESET researchers have named the group GopherWhisper and tied it to an intrusion at a Mongolian governmental entity. The name draws on two elements: most of the group’s tooling is written in Go, whose mascot is a gopher, and one of its side-loaded components ships as whisper.dll.
A toolset built mostly in Go
GopherWhisper operates a set of custom loaders, injectors, and backdoors. The Go-based components include three backdoors, LaxGopher, RatGopher, and BoxOfFriends, along with the JabGopher injector, the CompactGopher exfiltration utility, and the FriendDelivery loader. A C++ backdoor called SSLORDoor rounds out the arsenal.
Each backdoor pairs with a different legitimate service for command and control. LaxGopher pulls instructions from a private Slack workspace and posts results back to the same channel. RatGopher mirrors that design on Discord. BoxOfFriends takes a different route, using the Microsoft Graph API to exchange commands through Outlook draft messages. SSLORDoor communicates directly with the operators over an encrypted channel on port 443.
The supporting tools handle the rest of the chain. JabGopher and FriendDelivery load the backdoors into memory, and CompactGopher packages selected files and ships them out through the file.io sharing service.
Operator messages pulled from Slack, Discord, and Outlook
The group’s reliance on commercial platforms for C&C cut both ways. After recovering multiple Slack and Discord API tokens during analysis, ESET retrieved a large volume of operator traffic from those services.
“During our investigation, we managed to extract thousands of Slack and Discord messages, as well as several draft email messages from Microsoft Outlook. This gave us great insight into the inner workings of the group,” said ESET researcher Eric Howard, who discovered the new threat group.
The Slack channel tied to LaxGopher carried mostly disk and file enumeration commands. It also contained links to public GitHub repositories covering Go service installation, process injection on x86 and x64, and encryption and compression utilities. ESET assesses that operators consulted these repositories during development.
RatGopher’s Discord channel held Go source code that appears to be an earlier iteration of the backdoor, along with output from enumeration runs on operator machines. One of those machines was a VMware virtual machine whose install and boot timestamps line up with UTC+8.
Message timestamps from both Slack and Discord cluster between 8 a.m. and 5 p.m. UTC+8, matching China Standard Time. The configured user locale in Slack metadata pointed to the same zone, supporting the China-aligned attribution.
Outlook drafts reveal an infrastructure timeline
Extraction of Outlook content exposed operational housekeeping failures on the attacker side. The welcome email from Microsoft, sent when the mailbox was provisioned, remained in place. That message confirmed that the account barrantaya.1010@outlook[.]com was created on July 11, 2024. The FriendDelivery DLL that loads BoxOfFriends was compiled 11 days later, on July 22, 2024.
Investigators also determined that the Slack and Discord servers began life as test environments for the backdoors, and were later pressed into service as live C&C channels for LaxGopher and RatGopher across multiple compromised systems. Logs from the testing phase were never cleared, giving defenders a longer window into the group’s development and deployment activity.
ESET has published indicators of compromise in its GitHub repository.

Guide: Breach and Attack Simulation & Automated Penetration Testing