Signal responds to phishing attacks with new in-app security warnings
Signal is adding new protections for users following recent phishing and social engineering attacks.
In March, the FBI and CISA issued a warning stating that Signal had become a primary target of Russian intelligence-linked hackers.
Dutch and German security authorities were among the first to identify phishing campaigns targeting Signal users.
The scheme centered on Signal’s “linked devices” feature. Attackers contacted targets while posing as trusted entities, including support teams or known contacts.
Victims were then prompted to scan a QR code or approve a device-linking request. Once approved, the attacker’s device became linked to the account, allowing messages to be read as they were sent and received.
In other cases, attackers attempted to take over accounts by persuading users to share one-time verification codes or PINs, often under the guise of a security-related request.
“To help protect Signal users from phishing and social engineering attacks, we’ve introduced additional confirmations and educational messaging in the app to help people better detect fraudulent profiles, especially message requests from scammers posing as Signal,” the company wrote.
One of the new protections is an additional warning informing users that profile names on Signal are not verified and can be chosen freely by account holders, making impersonation attempts easier.
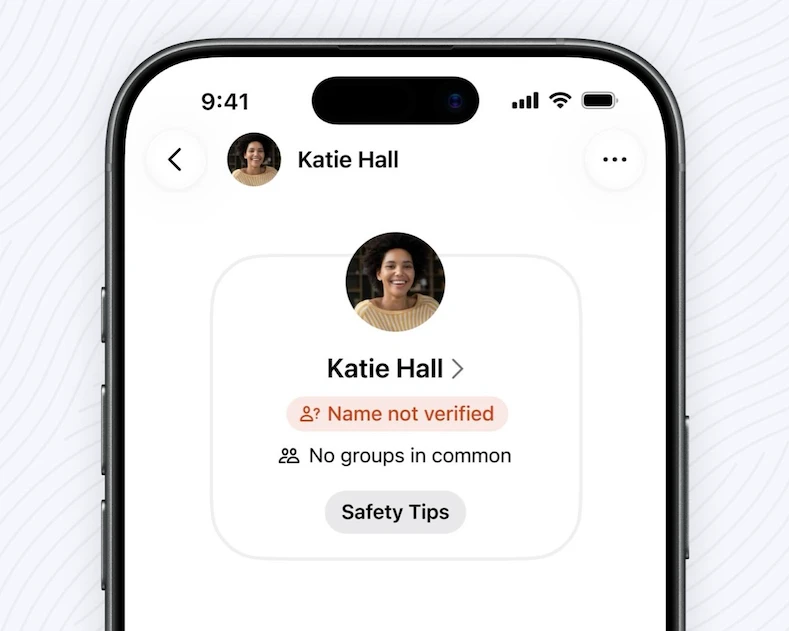
“Name not verified” feature (Source: Signal)
Signal also introduced an extra confirmation step when users accept message requests. After the initial request screen, a second prompt reminds users to only accept requests from trusted contacts and warns that Signal will never ask for registration codes, PINs, or recovery keys.
Additional changes include expanded in-app safety tips advising users not to respond to chats claiming to be from Signal, carefully review profile names and photos, and remain alert for phishing and impersonation scams.
Signal added that “more changes are on the way.”