Anamarija Pogorelec

Identity security planning for 2026 is shifting under pressure
Identity security planning is becoming more focused on scale, governance, and operational strain, according to the Identity Security Outlook 2026 report. The ManageEngine …

The roles and challenges in moving to quantum-safe cryptography
A new research project examines how organizations, regulators, and technical experts coordinate the transition to quantum safe cryptography. The study draws on a structured …

Product showcase: Blokada for Android gives users control over network traffic
Blokada is a network privacy and ad-blocking application available on Android, iOS, Windows, macOS, and Linux. It is designed to reduce ads, block trackers, and limit unwanted …

What security teams miss in email attacks
Email remains the most common entry point for attackers. This article examines how phishing, impersonation, and account takeover continue to drive email breaches and expose …

AI security risks are also cultural and developmental
Security teams spend much of their time tracking vulnerabilities, abuse patterns, and system failures. A new study argues that many AI risks sit deeper than technical flaws. …

Hospitals are drowning in threats they can’t triage
Healthcare is facing a rise in cyber threats driven by vulnerable medical devices, growing data exposure, and AI adoption. This article outlines the pressures, gaps, and …

What consumers expect from data security
Security teams spend years building controls around data protection, then a survey asks consumers a simple question about responsibility and the answer lands close to home. …

Ransomware’s new playbook is chaos
Ransomware threats are accelerating in scale, sophistication, and impact. Data reveals how evolving techniques, shifting payment trends, and AI-driven capabilities are …
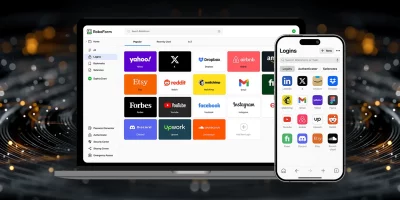
Product showcase: RoboForm password manager for iOS
RoboForm is a password manager that helps users store and manage login credentials, identities, and other sensitive information in one place. The app is available on macOS, …

Executives say cybersecurity has outgrown the IT department
Cybersecurity has moved from a technical problem to a boardroom concern tied to survival. A global Rimini Street study of senior executives shows security risk shaping …

Security teams debate how much to trust AI
AI is reshaping how organizations operate, defend systems, and interpret risk. Reports reveal rising AI-driven attacks, hidden usage across enterprises, and widening gaps …

Automation forces a reset in security strategy
Enterprise security teams are working under the assumption that disruption is constant. A global study by Trellix shows that resilience has moved from a long term goal to a …
Featured news
Resources
Don't miss
- ClickFix campaign delivers Mac malware via fake Apple page
- Poisoned “Office 365” search results lead to stolen paychecks
- What vibe hunting gets right about AI threat hunting, and where it breaks down
- Health insurance lead sites sell personal data within seconds of form submission
- Claude helps researcher dig up decade-old Apache ActiveMQ RCE vulnerability (CVE-2026-34197)