Anamarija Pogorelec

Bug bounties are broken, and the best security pros are moving on
Penetration testing engagements are organized as scheduled contracts with defined scope, set testing windows, and direct communication channels with client teams. Cobalt’s …

Cybersecurity jobs available right now: March 10, 2026
Associate Director Application Security BioNTech | Germany | On-site – View job details As an Associate Director Application Security, you will lead application security …

OpenWrt 25.12.0 ships with new package manager, built-in upgrade tool, support for 2200+ devices
OpenWrt 25.12.0 is now available for download. The release incorporates over 4,700 commits since branching from OpenWrt 24.10. Package manager changes One of the most …

More AI tools, more burnout! New research explains why
Workflows built around multiple AI agents and constant tool switching are adding cognitive strain across large enterprises. A recent Harvard Business Review analysis describes …

Open-source tool Sage puts a security layer between AI agents and the OS
Autonomous AI agents running on developer workstations execute shell commands, fetch URLs, and write files with little or no inspection of what they are doing. Open-source …
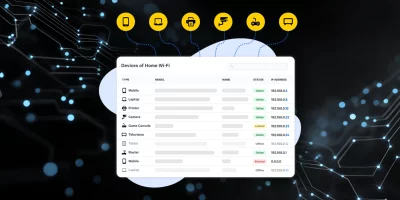
Product showcase: Fing Desktop puts network visibility on your screen
Phones, laptops, smart TVs, cameras, and smart home equipment all use the same network. Knowing what’s connected helps users manage performance and security. Fing Desktop …

Submarine cables move to the center of critical infrastructure security debate
The cables running along the ocean floor carry the overwhelming majority of the world’s cross-border data traffic, and for most of their operational history they have …

New cyber module strengthens risk planning for health organizations
The Administration for Strategic Preparedness and Response’s (ASPR) new cybersecurity module in the Risk Identification and Site Criticality (RISC) 2.0 Toolkit helps …
Cursor Automations turns code review and ops into background tasks
Cursor Automations, the always-on agent platform from Cursor, is expanding with a new generation of autonomous systems that streamline code review, incident response, and …

What happens when AI teams compete against human hackers
A cybersecurity competition produced what may be the largest controlled dataset comparing AI-augmented teams to human-only teams on professional-grade offensive security …

New infosec products of the week: March 6, 2026
Here’s a look at the most interesting products from the past week, featuring releases from Beazley Security, Push Security, Samsung, and Tufin. Samsung brings Digital Home Key …

That attractive online ad might be a malware trap
Malware increasingly travels through the infrastructure that delivers online advertising. The Media Trust’s Global Report on Digital Trust, Ad Integrity, and the Protection of …
Featured news
Resources
Don't miss
- ClickFix campaign delivers Mac malware via fake Apple page
- Poisoned “Office 365” search results lead to stolen paychecks
- What vibe hunting gets right about AI threat hunting, and where it breaks down
- Health insurance lead sites sell personal data within seconds of form submission
- Claude helps researcher dig up decade-old Apache ActiveMQ RCE vulnerability (CVE-2026-34197)