Mirko Zorz

Top product launches at RSAC 2026
RSAC 2026 showcased a wave of innovation, with vendors unveiling technologies poised to redefine cybersecurity. From AI-powered defense to breakthroughs in identity …

AI SOC vendors are selling a future that production deployments haven’t reached yet
Vendors selling AI-powered security operations platforms have built their pitches around a consistent set of promises: autonomous threat investigation, dramatic reductions in …

A nearly undetectable LLM attack needs only a handful of poisoned samples
Prompt engineering has become a standard part of how large language models are deployed in production, and it introduces an attack surface most organizations have not yet …

Your facilities run on fragile supply chains and nobody wants to admit it
In this Help Net Security interview, Christa Dodoo, Global Chair at IFMA, discusses how facility managers are managing supply chain risk in critical building systems. She …

Training an AI agent to attack LLM applications like a real adversary
Most enterprise software development teams now ship AI-powered applications faster than traditional penetration testing can keep up with. A security team with 500 applications …

The AI safety conversation is focused on the wrong layer
Organizations have spent years accumulating fragmented identity systems: too many roles, too many credentials, too many disconnected tools. For a workforce of humans, that …
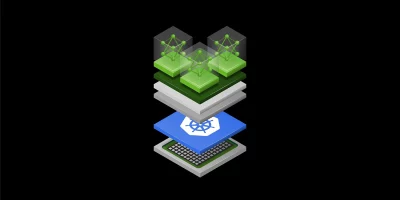
NVIDIA puts GPU orchestration in community hands
GPU-accelerated AI workloads now run on Kubernetes in the large majority of enterprise environments. Managing those workloads at scale has required specialized tooling that, …

Measuring security performance in real-time, not once a quarter
Most organizations have invested heavily in security products over the past decade. The assumption embedded in that spending is that more tools equal better protection. Tim …

Quantum threats are already active and the defense response remains fragmented
Enterprises are moving toward post-quantum security at uneven speeds, and the gap between organizations that have built crypto-agility into their infrastructure and those that …

Top must-visit companies at RSAC 2026
RSAC 2026 Conference is taking place at the Moscone Center in San Francisco March 23 – 26. With hundreds of booths, countless product demos, and nonstop buzz, navigating …

Your AI agents are moving sensitive data. Do you know where?
In this Help Net Security interview, Gidi Cohen, CEO at Bonfy.AI, addresses what he sees as the most pressing gap in AI agent security: data-layer risk. While the industry …

NIST updates its DNS security guidance for the first time in over a decade
DNS infrastructure underpins nearly every network connection an organization makes, yet security configurations for it have gone largely unrevised at the federal guidance …
Featured news
Resources
Don't miss
- Sandyaa: Open-source autonomous security bug hunter
- The hidden risk of non-human identities in AI adoption
- Researchers open-source a Wi-Fi cyber range for security training
- Android pushes new scam, theft, and AI protections in 2026 update wave
- Microsoft May 2026 Patch Tuesday: Many fixes, but no zero-days